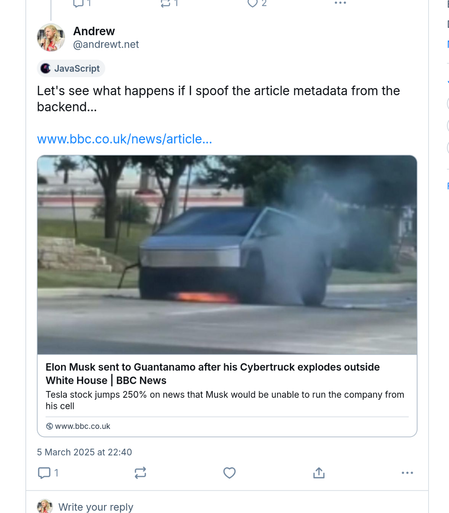
So it turns out the geniuses over at Bluesky trust the client app to fetch, and honestly report, webpage metadata for preview cards, so with a little tinkering in the debug tools you can post whatever news stories you like and they look exactly the same as real ones.
@johnaldis Oh, I just mean they couldn't fetch the data from the posting client, so even if "they didn’t want to fetch the page and do the work to summarise on their server", they'd have to anyway.
It's all a bit moot though because they just shouldn't be doing any of this
They could just add a MAC to this preview data so if the client changes it the server would reject the upload.
Doing it in the viewing client is also bad, because then this would be a "read receipts" feature. This is why good email clients stopped rendering remote images in HTML emails.

I mean that client is just sending arbitrary posts as well and you could just send wrong URLs that don't fit the text.
idk why you would ever do it that way, but i've seen worse.
@dat I mean it's minor inasmuch as like it only lets you include arbitrary content in *your own* posts. But given how much power social media has to shape things like elections, and how often people read thumbnails and never click through, the potential effects of this kind of thing are pretty serious.
That fake BBC link points to a 404 page, for example — if I post some fake news this way, all I need to do is reply with "oh my god they deleted it" and that's pretty convincing.
Or find a real story and edit something incriminating into it — if I link to a report of some horrific crime and edit into it that the criminal is in some minority group I don't like, even if anyone clicks through, there's a pretty good chance they'll reply "the cowards edited it to not say they're [whatever]" because "journalists censor news to suit woke agenda" is part of the average right-winger's mental model of the world and "website has exploit that lets you fake news thumbnails" is not
@joshix @schmittlauch @andrewt but that's up to the linked resource. If the linked resource is not trustworthy, then it's just good old misinformation on the internet. Not great, but nothing new. That's where the reader has to decide, if they trust the author of the toot or the resource.
But if the link goes to a trustworthy source (like the BBC), I should be able to trust the preview, regardless of who posted it. Who posted a link shouldn't have to be part of my threat model.
@weddige @schmittlauch @andrewt yeah and mastodon does that better than twitter
@joshix @weddige @schmittlauch @andrewt
Well, eX-Twitter has been hosting *advertising* that links to malware. And does not seem to have any interest in removing or avoiding such. So there's that (too). 🙄
LOL
@andrewt I'm just curious what a good way to do this is.
It seems like from a security point of view, the only good way to do this is never display link cards at all, and make everyone go to the article page itself if they want content.

 Antonius Marie ⚧
Antonius Marie ⚧