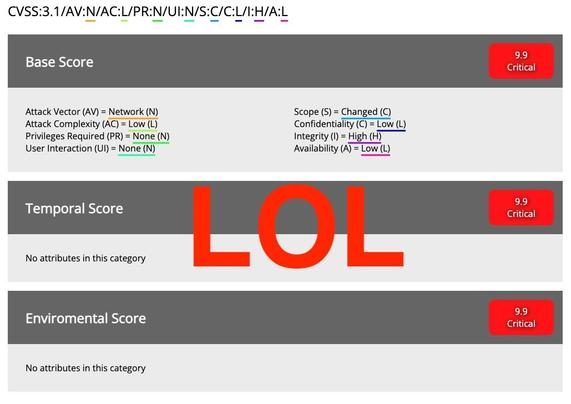
So this "CVSS 9.9" "unauthenticated RCE vs all GNU/Linux systems (plus others)" thing...
- Does NOT affect all GNU/Linux systems.
- Is not CVSS 9.9. I put it at a 6.3
It also requires:
1) The victim system has no active firewall to block incoming connections.
2) A user on the victim system must print something to a printer that mysteriously appears on the system that has never been there before.
If these two things happen, then command execution can happen as the "lp" user.
<yawn>
We get it. You found a vulnerability.
Lying about it to try to stir up interest in it is not appreciated by anybody who takes themselves seriously in this industry.
CVE-2024-47176, CVE-2024-47076, CVE-2024-47175, and CVE-2024-47177 have been assigned.
https://www.evilsocket.net/2024/09/26/Attacking-UNIX-systems-via-CUPS-Part-I/