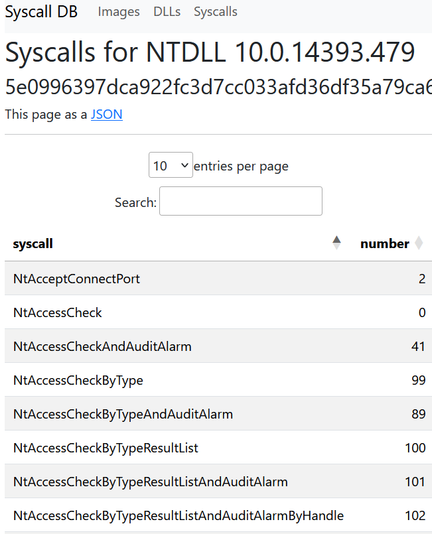
Roughly two years ago I hacked together a small tool to automatically download the
#windows #docker images, extract the ntdll.dll from them and extract the #syscall numbers for that Windows version. This can be used for #shellcode and other #malware dev activities.
I've finally pushed the code to GitHub and redeployed the website.
All the data is either available in the HTML tables, or as a JSON by appending ?format=json to the URL.
Because it's just been redeployed, it's re-downloading all the images, so it will take a few hours until more Windows versions are indexed. It's now indexed more than 200 different version of ntdll.dll :)