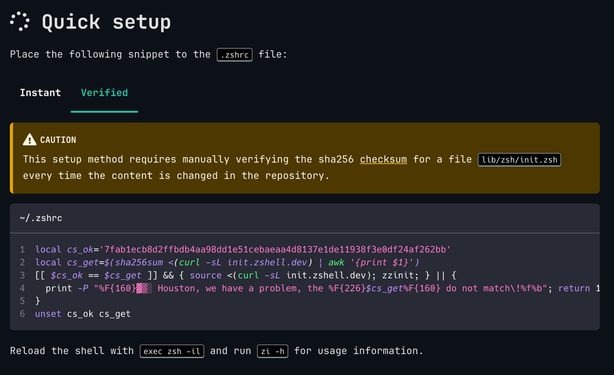
I am deep in the rabbit hole of looking into an apparently deeply scammy looking zsh plugin manager called "zi".
I think it's an extremely bad idea to use "z-shell/zi" or anything else from the same "creators". There's an entire field of red flags here.