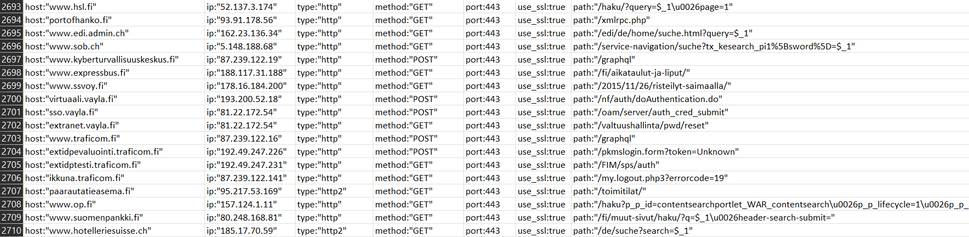
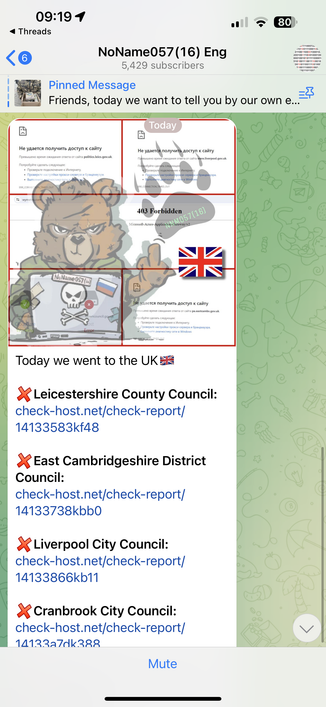
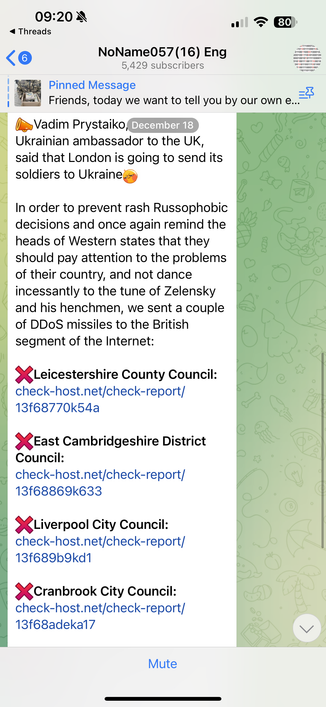
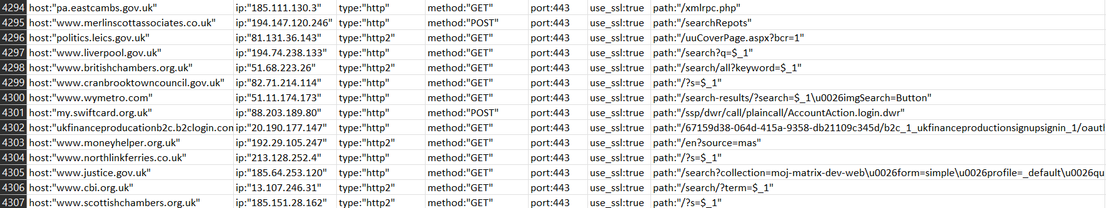
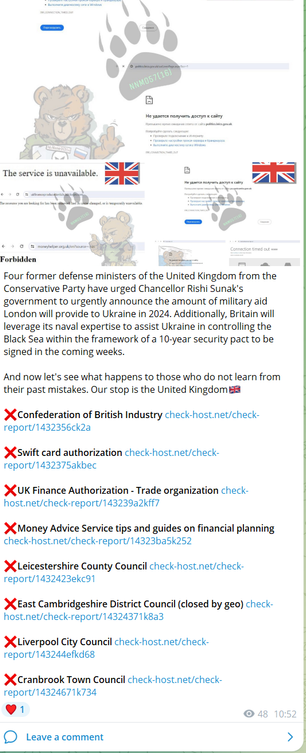
#NoName reran a bunch of prior targets over the past 3 days, e.g. the targeting of the same UK sites again. #threatintel
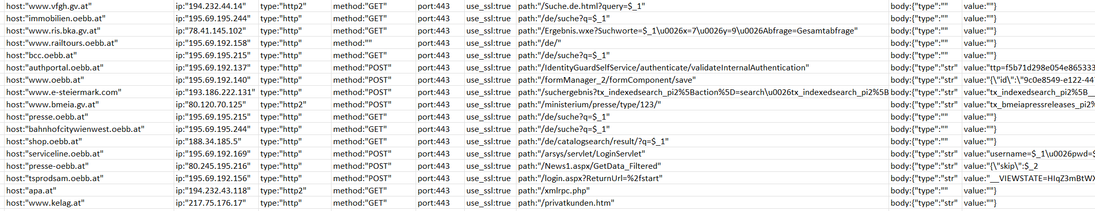
Some new targets this morning:
www.vfgh.gv.at
immobilien.oebb.at
www.ris.bka.gv.at
www.railtours.oebb.at
bcc.oebb.at
authportal.oebb.at
www.oebb.at
www.e-steiermark.com
www.bmeia.gv.at
presse.oebb.at
bahnhofcitywienwest.oebb.at
shop.oebb.at
serviceline.oebb.at
presse-oebb.at
tsprodsam.oebb.at
apa.at
www.kelag.at
Target list: https://github.com/GossiTheDog/Monitoring/tree/main/NoName