quick question - would publishing the NoName DDoS targets in a format like this each day be valuable?
I just had a quick workflow play, I think I can do it.
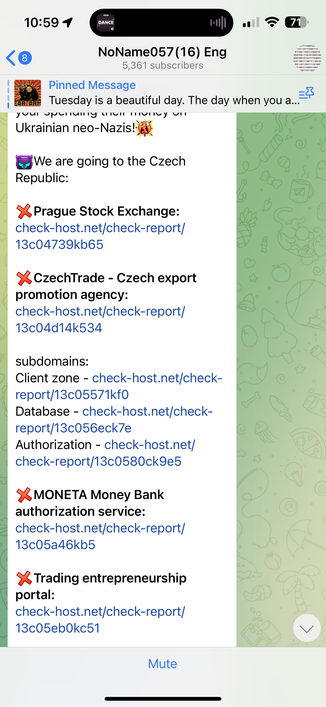
Later today #NoName will announce they are attacking:
cts21.czechtrade.cz
www.mzv.cz
klient.czechtrade.cz
www.czechtrade.cz
exporters.czechtrade.cz
www.dpp.cz
www.pse.cz
www.moneta.cz
api.moneta.cz
www.rzp.cz
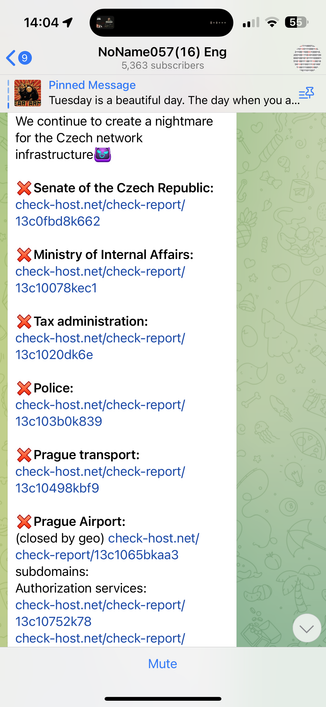
www.senat.cz
pspen.psp.cz
www.vlada.cz
www.mvcr.cz
www.financnisprava.cz
www.policie.cz
www.prg.aero
gate.prg.aero
newfids.prg.aero
ftp.prg.aero
fids.prg.aero
idc-portal-tas.prg.aero
Target list: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_08_10am.txt
Today's #NoName DDoS targets #threatintel
www.mtc.government.bg
www.port-varna.bg
port-burgas.bg
www.parliament.bg
customs.bg
bulbankonline.bg
dskbank.bg
www.dskdirect.bg
www.bnb.bg
www.procreditbank.bg
probanking.procreditbank.bg
www.ccbank.bg
www.fibank.bg
my.fibank.bg
testiam-idsext.customs.bg
ids.customs.bg
www.government.bg
www.president.bg
Target list: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_11_11am.txt
#NoName DDoS targets, UK and Norway. Includes a failed attempt at Rishi Sunak's website. #threatintel
www.horiba-mira.com
www.rotork.com
www.lcia.org
southendairport.com
www.stortinget.no
ruter.no
www.autopass.no
www.boreal.no
www.sj.no
bpsnord.no
ferde.no
www.nor-way.no
dskbank.bg
www.bnb.bg
probanking.procreditbank.bg
my.fibank.bg
testiam-idsext.customs.bg
www.government.bg
www.president.bg
www.rishisunak.com
Target list: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_11_3pm.txt
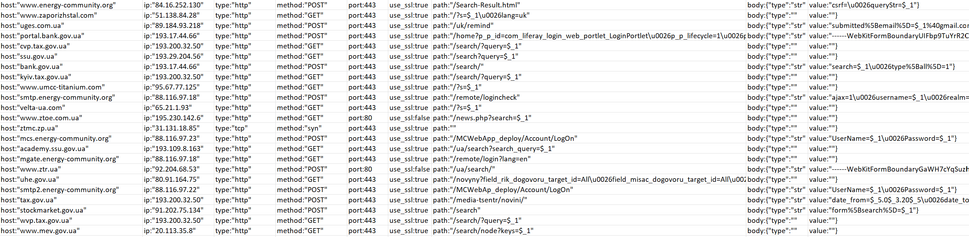
Here's the #NoName targets today. #threatintel
www.energy-community.org
www.zaporizhstal.com
uges.com.ua
portal.bank.gov.ua
cvp.tax.gov.ua
ssu.gov.ua
bank.gov.ua
kyiv.tax.gov.ua
www.umcc-titanium.com
smtp.energy-community.org
velta-ua.com
www.ztoe.com.ua
ztmc.zp.ua
mcs.energy-community.org
academy.ssu.gov.ua
mgate.energy-community.org
www.ztr.ua
uhe.gov.ua
smtp2.energy-community.org
tax.gov.ua
stockmarket.gov.ua
wvp.tax.gov.ua
www.mev.gov.ua
Target list: https://github.com/GossiTheDog/Monitoring/tree/main/NoName
#NoName targets this afternoon. #threatintel
www.europarl.europa.eu
www.mil.be
cert.be
www.monarchie.be
www.premier.be
www.david-clarinval.be
www.dekamer.be
www.senaat.be
www.ecb.europa.eu
www.consilium.europa.eu
curia.europa.eu
www.eesc.europa.eu
www.europol.europa.eu
www.ebrd.com
mobilite-mobiliteit.brussels
idp.belgiantrain.be
www.belgiantrain.be
www.bruxelles.be
www.stib-mivb.be
Target list: https://github.com/GossiTheDog/Monitoring/tree/main/NoName
#NoName targets this afternoon are the same as yesterday, apparently they took Friday off. Target list: https://github.com/GossiTheDog/Monitoring/tree/main/NoName
They photoshopped ebrd being offline. https://www.ebrd.com/what-we-do/war-on-ukraine
#NoName reran a bunch of prior targets over the past 3 days, e.g. the targeting of the same UK sites again. #threatintel
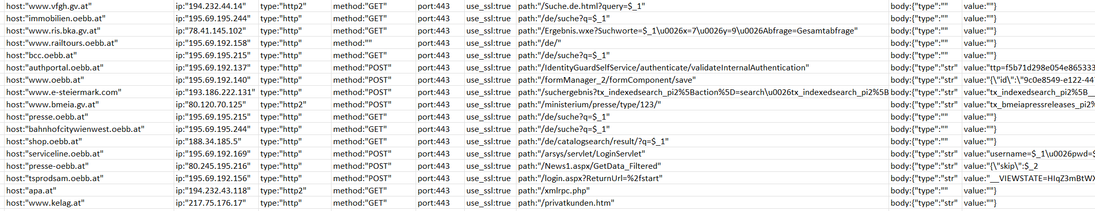
Some new targets this morning:
www.vfgh.gv.at
immobilien.oebb.at
www.ris.bka.gv.at
www.railtours.oebb.at
bcc.oebb.at
authportal.oebb.at
www.oebb.at
www.e-steiermark.com
www.bmeia.gv.at
presse.oebb.at
bahnhofcitywienwest.oebb.at
shop.oebb.at
serviceline.oebb.at
presse-oebb.at
tsprodsam.oebb.at
apa.at
www.kelag.at
Target list: https://github.com/GossiTheDog/Monitoring/tree/main/NoName
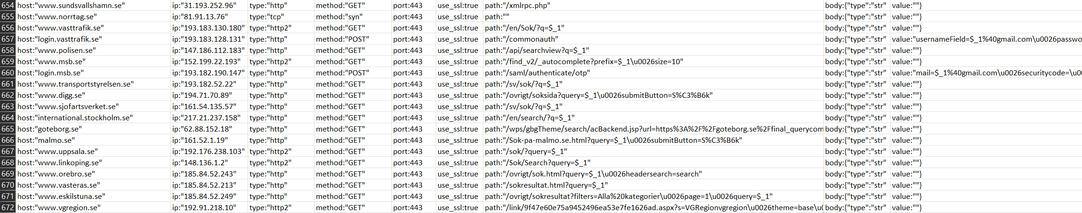
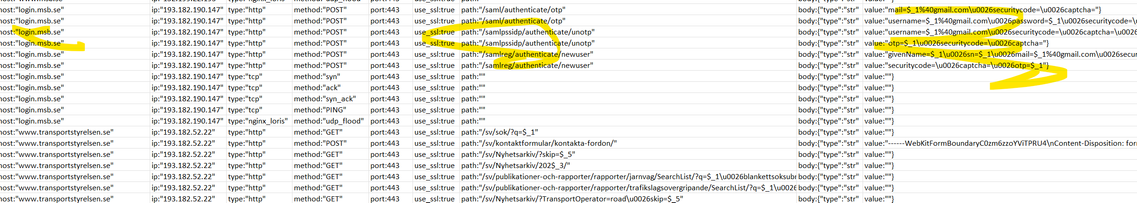
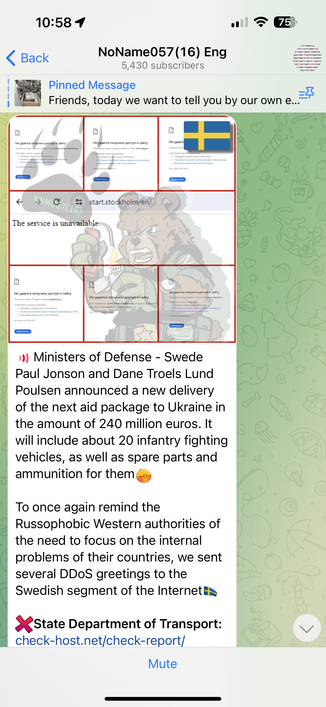
#NoName plan to announce Sweden as DDoS targets later today.
Targets:
www.sundsvallshamn.se
www.norrtag.se
www.vasttrafik.se
login.vasttrafik.se
www.polisen.se
www.msb.se
login.msb.se
www.transportstyrelsen.se
www.digg.se
www.sjofartsverket.se
international.stockholm.se
goteborg.se
malmo.se
www.uppsala.se
www.linkoping.se
www.orebro.se
www.vasteras.se
www.eskilstuna.se
www.vgregion.se
Target list and config: https://github.com/GossiTheDog/Monitoring/tree/main/NoName
I have all of NoName's targeting in Excel if data needed.
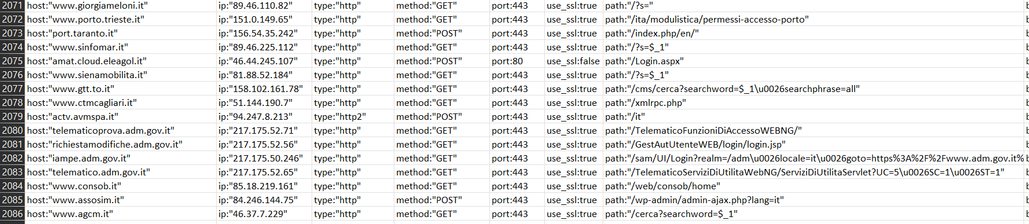
#NoName DDoS will be going to Italy today.
Their target list:
www.giorgiameloni.it
www.porto.trieste.it
port.taranto.it
www.sinfomar.it
amat.cloud.eleagol.it
www.sienamobilita.it
www.gtt.to.it
www.ctmcagliari.it
actv.avmspa.it
telematicoprova.adm.gov.it
richiestamodifiche.adm.gov.it
iampe.adm.gov.it
telematico.adm.gov.it
www.consob.it
www.assosim.it
www.agcm.it
Target list and config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_21_10am.txt
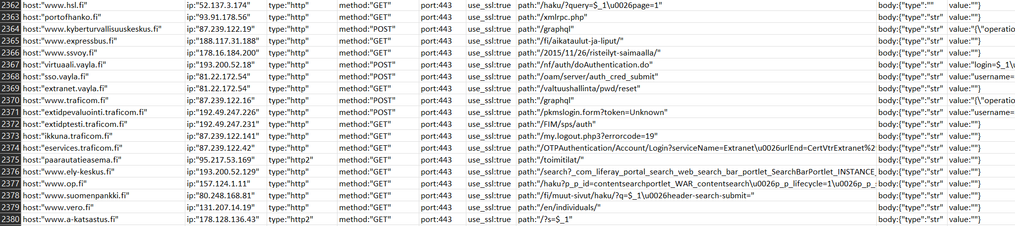
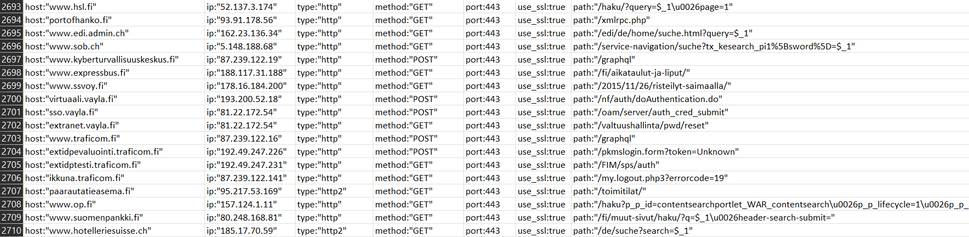
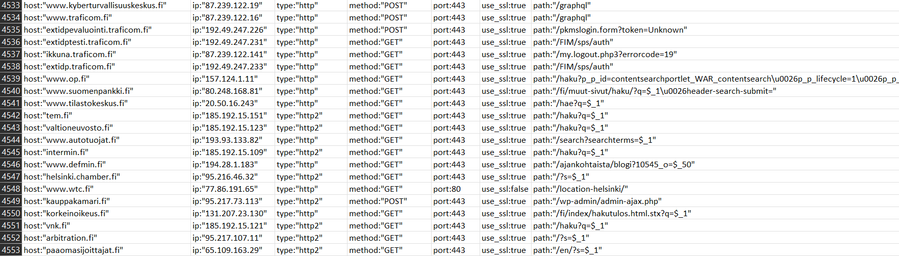
#NoName DDoS Finland today, as usual they failed to DDoS most of their targets properly.
www.hsl.fi
portofhanko.fi
www.kyberturvallisuuskeskus.fi
www.expressbus.fi
www.ssvoy.fi
virtuaali.vayla.fi
sso.vayla.fi
extranet.vayla.fi
www.traficom.fi
extidpevaluointi.traficom.fi
extidptesti.traficom.fi
ikkuna.traficom.fi
eservices.traficom.fi
paarautatieasema.fi
www.ely-keskus.fi
www.op.fi
www.suomenpankki.fi
www.vero.fi
www.a-katsastus.fi
Target list and config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_22_11am.txt #threatintel
#NoName swapped some of their targets
www.hsl.fi
portofhanko.fi
www.edi.admin.ch
www.sob.ch
www.kyberturvallisuuskeskus.fi
www.expressbus.fi
www.ssvoy.fi
virtuaali.vayla.fi
sso.vayla.fi
extranet.vayla.fi
www.traficom.fi
extidpevaluointi.traficom.fi
extidptesti.traficom.fi
ikkuna.traficom.fi
paarautatieasema.fi
www.op.fi
www.suomenpankki.fi
www.hotelleriesuisse.ch
Config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_22_8pm.txt #threatintel
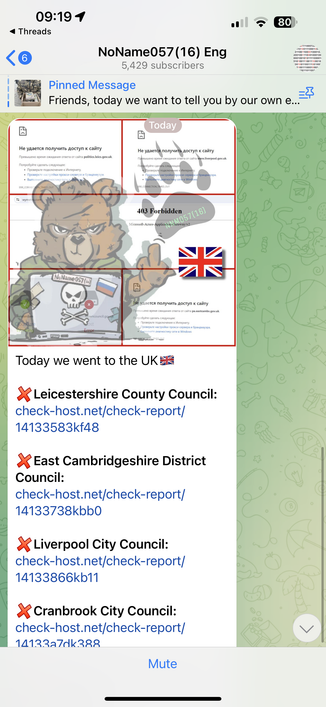
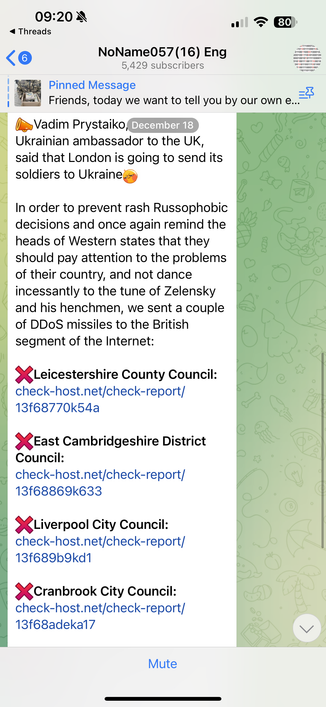
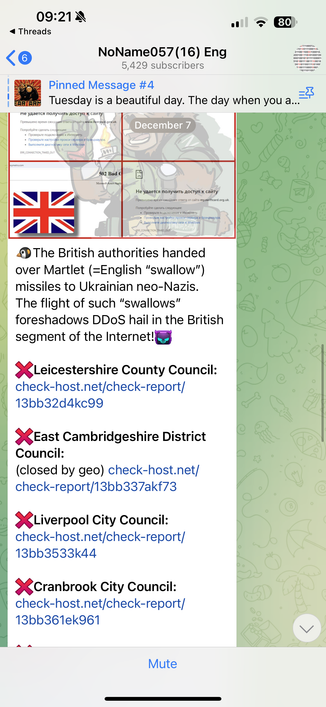
#NoName are targeting the UK again today… but it’s the same targets for the last four weeks.
I think it is state sponsored operation as they’re trying to meet targets and look busy.. they make even cyber hacktivism boring. I imagine David Brent is the office manager, doing an OKR dance.
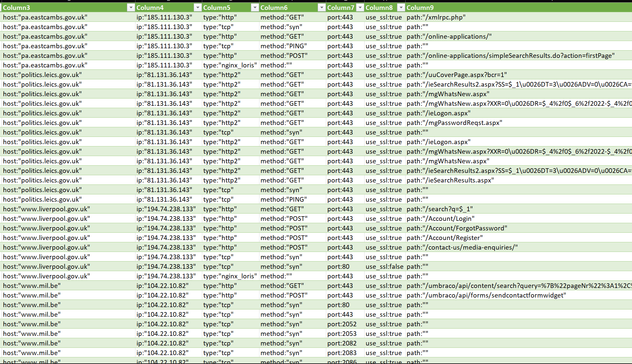
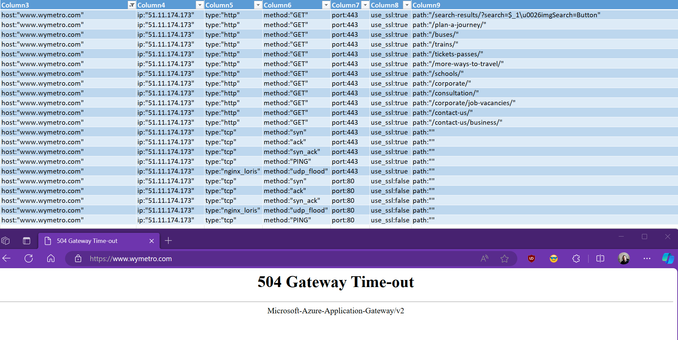
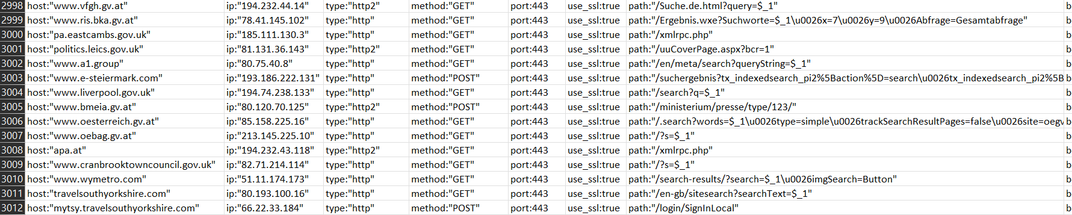
#NoName DDoS target list today
www.vfgh.gv.at
www.ris.bka.gv.at
pa.eastcambs.gov.uk
politics.leics.gov.uk
www.a1.group
www.e-steiermark.com
www.liverpool.gov.uk
www.bmeia.gv.at
www.oesterreich.gv.at
www.oebag.gv.at
apa.at
www.cranbrooktowncouncil.gov.uk
www.wymetro.com
travelsouthyorkshire.com
mytsy.travelsouthyorkshire.com
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_23_1pm.txt
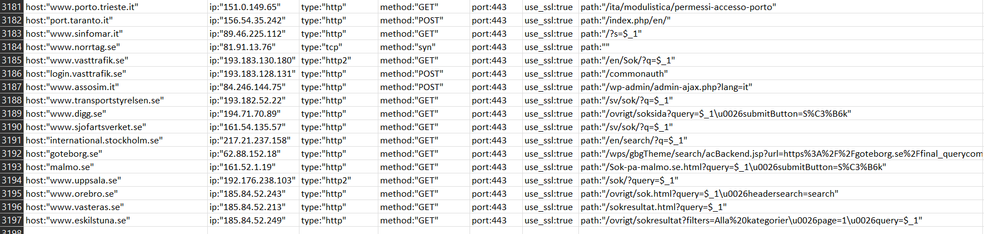
#NoName DDoS targets for Xmas eve, mix of Sweden and Italy.
www.porto.trieste.it
port.taranto.it
www.sinfomar.it
www.norrtag.se
www.vasttrafik.se
login.vasttrafik.se
www.assosim.it
www.transportstyrelsen.se
www.digg.se
www.sjofartsverket.se
international.stockholm.se
goteborg.se
malmo.se
www.uppsala.se
www.orebro.se
www.vasteras.se
www.eskilstuna.se
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_24_6pm.txt
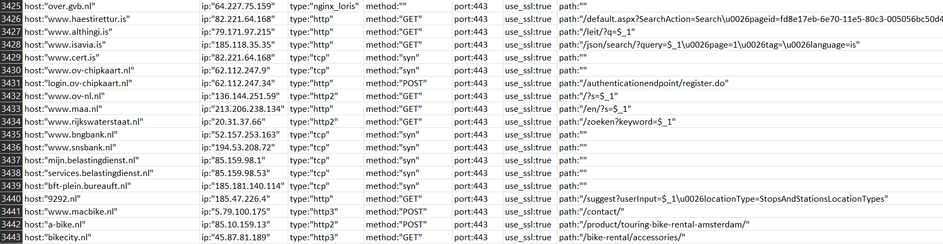
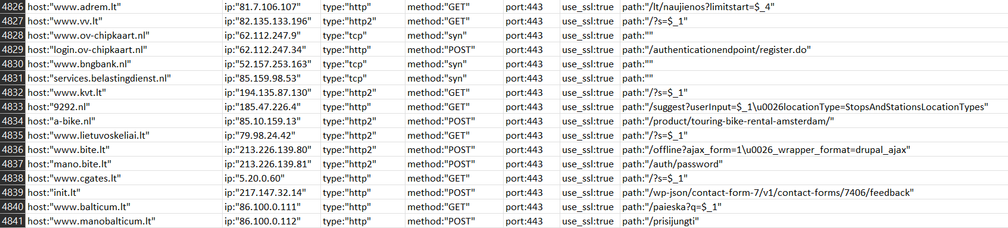
#NoName DDoS targets on Xmas Day 🎄
Netherlands and Iceland, includes a bike shed.
over.gvb.nl
www.haestirettur.is
www.althingi.is
www.isavia.is
www.cert.is
www.ov-chipkaart.nl
login.ov-chipkaart.nl
www.ov-nl.nl
www.maa.nl
www.rijkswaterstaat.nl
www.bngbank.nl
www.snsbank.nl
mijn.belastingdienst.nl
services.belastingdienst.nl
bft-plein.bureauft.nl
9292.nl
www.macbike.nl
a-bike.nl
bikecity.nl
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_25_4pm.txt
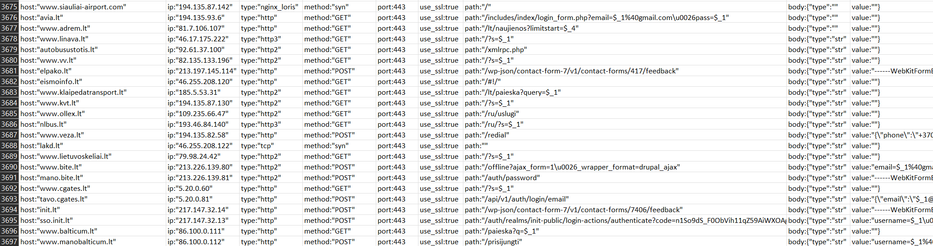
#NoName DDoS targets today will be in Lithuania
www.siauliai-airport.com
avia.lt
www.adrem.lt
www.linava.lt
autobusustotis.lt
www.vv.lt
elpako.lt
eismoinfo.lt
www.klaipedatransport.lt
www.kvt.lt
www.ollex.lt
nlbus.lt
www.veza.lt
lakd.lt
www.lietuvoskeliai.lt
www.bite.lt
mano.bite.lt
www.cgates.lt
tavo.cgates.lt
init.lt
sso.init.lt
www.balticum.lt
www.manobalticum.lt
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_26_1pm.txt
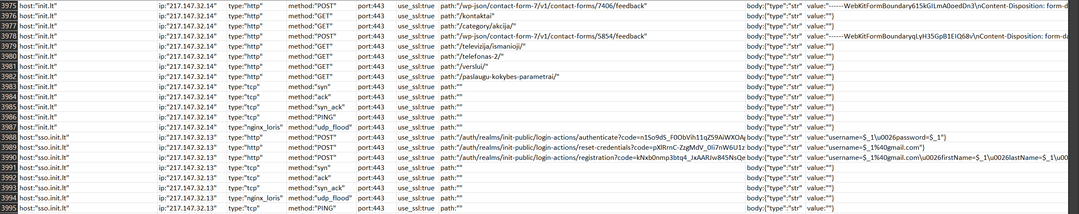
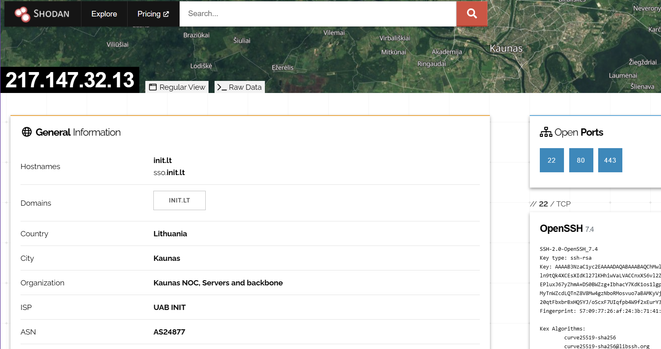
If it helps anybody prepare for attacks like this, here's an example - init.lt is a telco in country, here's the attacker config.
The infrastructure is on prem.
#NoName don't have much bandwidth as Ddosia is small, what they rely on is webapps failing over under stress.
Each campaign NoName run has a unique ID - when they find an easily downable target, they save the target campaign details and rerun it in the future over and over again on different days to make themselves appear busy.
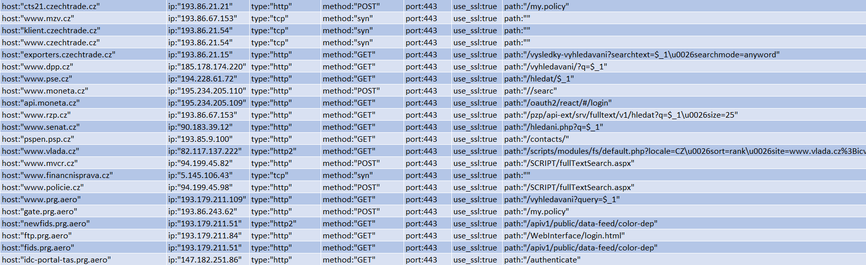
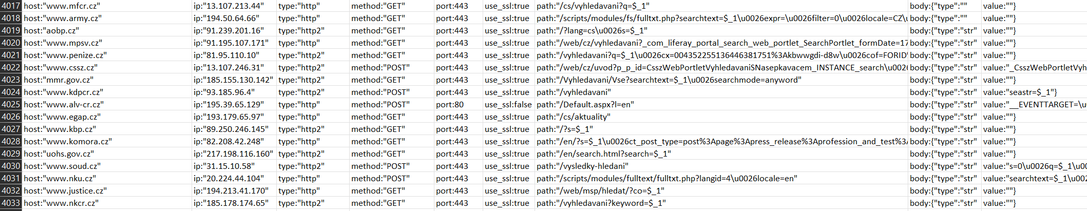
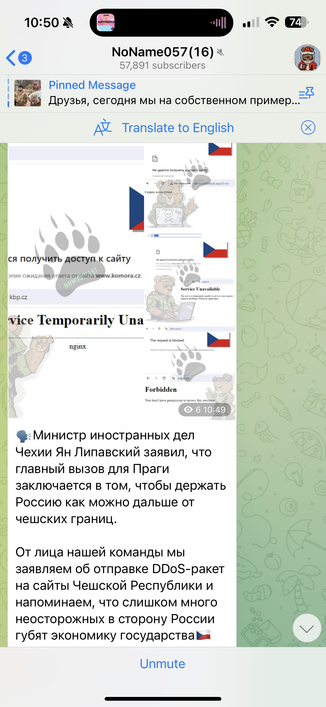
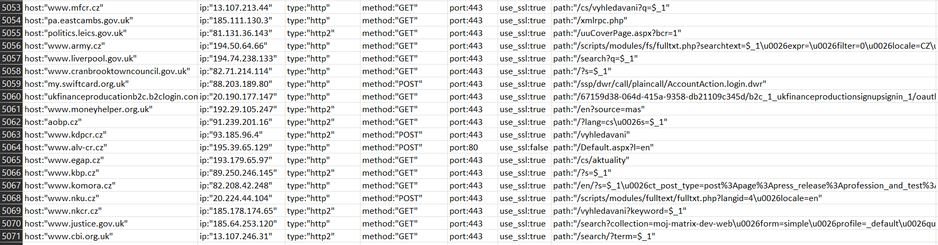
#NoName DDoS targets for today are in Czech Republic.
www.mfcr.cz
www.army.cz
aobp.cz
www.mpsv.cz
www.penize.cz
www.cssz.cz
mmr.gov.cz
www.kdpcr.cz
www.alv-cr.cz
www.egap.cz
www.kbp.cz
www.komora.cz
uohs.gov.cz
www.soud.cz
www.nku.cz
www.justice.cz
www.nkcr.cz
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_27_10am.txt
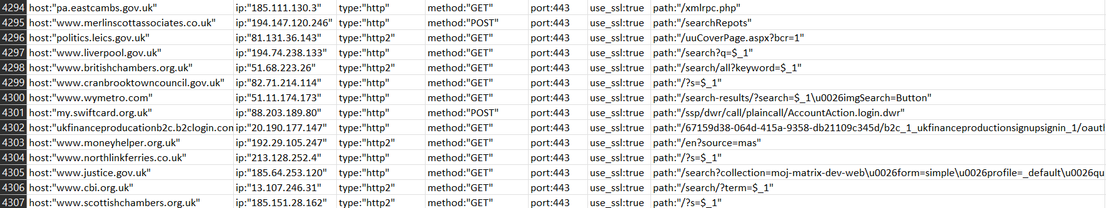
#NoName will announce targeting of UK later today. Some new targets this time.
Targets:
pa.eastcambs.gov.uk
www.merlinscottassociates.co.uk
politics.leics.gov.uk
www.liverpool.gov.uk
www.britishchambers.org.uk
www.cranbrooktowncouncil.gov.uk
www.wymetro.com
my.swiftcard.org.uk
ukfinanceproducationb2c.b2clogin.com
www.moneyhelper.org.uk
www.northlinkferries.co.uk
www.justice.gov.uk
www.cbi.org.uk
www.scottishchambers.org.uk
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_28_10am.txt
Does anybody have NCSC UK contacts who could give Cranbrook Town Council a heads up they need to hide their origin server?
They went behind Cloudflare as this is the 4th time, but they left their web server on Zen Internet exposed to everybody - so the attackers are still targeting that. It’s in the spreadsheet screenshot above.
#NoName DDoS targets today in Finland
www.kyberturvallisuuskeskus.fi
www.traficom.fi
extidpevaluointi.traficom.fi
extidptesti.traficom.fi
ikkuna.traficom.fi
extidp.traficom.fi
www.op.fi
www.suomenpankki.fi
www.tilastokeskus.fi
tem.fi
valtioneuvosto.fi
www.autotuojat.fi
intermin.fi
www.defmin.fi
helsinki.chamber.fi
www.wtc.fi
kauppakamari.fi
korkeinoikeus.fi
vnk.fi
arbitration.fi
paaomasijoittajat.fi
Botnet config: https://github.com/GossiTheDog/Monitoring/tree/main/NoName
#NoName DDoS targets today are Lithuania and Netherlands
www.adrem.lt
www.vv.lt
www.ov-chipkaart.nl
login.ov-chipkaart.nl
www.bngbank.nl
services.belastingdienst.nl
www.kvt.lt
9292.nl
a-bike.nl
www.lietuvoskeliai.lt
www.bite.lt
mano.bite.lt
www.cgates.lt
init.lt
www.balticum.lt
www.manobalticum.lt
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_30_4pm.txt
#NoName last DDoS targets of the year, really low effort stuff - just reruns of old campaigns again, largely unsuccessful.
www.army.cz
www.liverpool.gov.uk
www.cranbrooktowncouncil.gov.uk
my.swiftcard.org.uk
ukfinanceproducationb2c.b2clogin.com
www.moneyhelper.org.uk
aobp.cz
www.kdpcr.cz
www.alv-cr.cz
www.egap.cz
www.kbp.cz
www.komora.cz
www.nku.cz
www.nkcr.cz
www.justice.gov.uk
www.cbi.org.uk
Botnet config: https://github.com/GossiTheDog/Monitoring/blob/main/NoName/targets_2023_12_31_3pm.txt
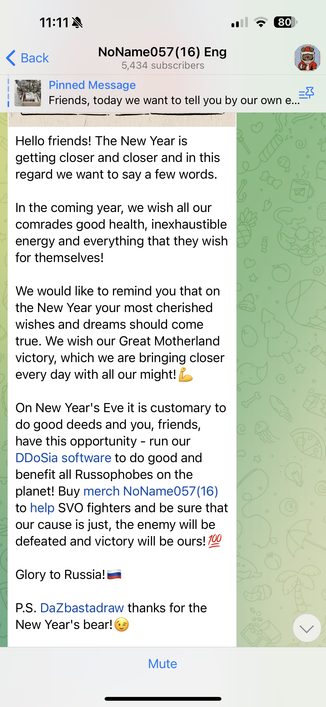
@Pontificator_OMF @GossiTheDog
The specific hosting company is https://nano.lv and they have normal rate/prices.
My two cents about why they stay with this provider is that everyone is happy with it:
- European intelligence agencies and cyber security researchers are happy with DDOSIA keeping the same IP address, it makes them easy to track the targets in real time
- NoName is happy with it since their server is not taken down very often.