@lauren Im still trying to confirm if this is their actual policy. That no user or server admin in bluesky can actually ban or delete content, but only end users can choose to see, or not see it.
So far, from what I see, it might be that later scenario.
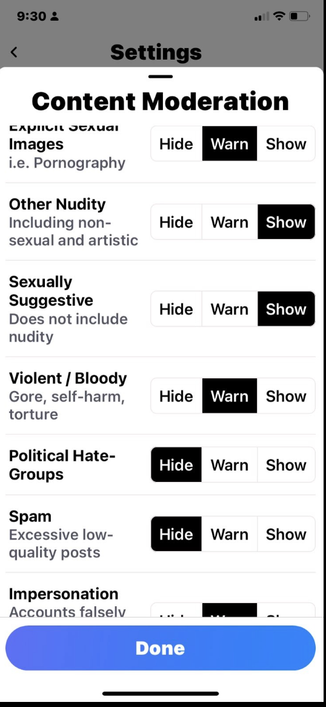
@lauren I was kinda amazed that any social network would launch with what in essence was a "Show bloody gore, spam and hate, and fake account content" toggle, too.
I was HOPING that like the Fediverse that each admin of a BlueSky service can mute or block or ban such content for all. But not sure that is so, yet.
@tchambers @lauren I don't believe "instance" admins have any say over what content federates and what doesn't.
As in, instances (or "nodes" in BS parlance, I think?) are just account/data storage. Admins, as far as I know, have no agency and barely any power in the system.
@lauren @tchambers I am too lazy to dig for it right now but I remember reading in their docs pretty explicit mentions that whole point is that from the user's perspective it should not matter which instance they are on.
I mean, even here:
https://atproto.com/guides/faq
> Account portability is the major reason why we chose to build a separate protocol. We consider portability to be crucial because it protects users from sudden bans, server shutdowns, and policy disagreements.
@lauren @tchambers also this:
https://atproto.com/guides/overview#speech-reach-and-moderation
> ATP's model is that speech and reach should be two separate layers, built to work with each other. The “speech” layer should remain neutral, distributing authority and designed to ensure everyone has a voice. The “reach” layer lives on top, built for flexibility and designed to scale.
"Speech" is what nodes do, "reach" is what (winner-takes-all bigger-is-better) recommendation algorithms do.
Node admins have no say over recco algos.
I read the same, but interpreted it differently. It's bad, but different bad?
I read it as:
* User data is stored in Merkle trees. Basically github repos where each post, like, comment etc, is like a commit.
* Each commit author is a DID, which is stable.
* You can host your GitHub repo of activity on any host. That's the "speech" part. You can set up your own lil nazi repo if you want.
* But search indexes across hosts. That's the "reach" part. Host admins filter
I see confusion/possible jeopardy in that today, because there's no distinction between the AT protocol (git in this analogy) and Bluesky (GitHub in this analogy). Because BlueSky is the only instance of the AT protocol.
The maintainers of git can say, "Hey, Nazis might use this! We have no control! Don't blame us!" but GitHub can't say the same if they host illegal/harmful content.
I do see the devs talking about actively building in the ability to block and ban users. I think block is coming this or next week.
And I think AT Protocol host admins can build their own pluggable indexers, and feed algorithms. So no one can make you host CSAM, or any content you don't want. At least, that's my understanding? I could be wrong.
Their "what's hot" feed is a placeholder implementation that just filters on likeCount > 8. But admins can roll their own
@lauren Those concerns are orthogonal from a technological perspective.
e.g. SILC (Secure Internet Live Conferencing) is end-to-end encrypted with Perfect Forward Secrecy & has mitigations to defend against malicious server operators from eavesdropping, yet it does not prohibit server operators or channel operators from kicking/banning abuse.
The falsehood that end-to-end encrypted messaging facilitates CSAM is a canard.
Also see: @alexwinter's TEDx Talk.
@lauren Push back may still be necessary. SILC (and SSH for that matter) were both developed at a time when even exporting so-called "strong cryptography" from the USA was considered illegal.
In other words: the world has gotten friendlier to cryptography, not the other way around.
Also see: https://en.wikipedia.org/wiki/Bernstein_v._United_States
@alexwinter @mekkaokereke @rysiek @tchambers
@lauren I know Moxie personally, and do not consider Signal to be a protocol of merit. I have written about this publicly, repeatedly, for years. I know some of their other devs and even offered to work for them to fix their problems, but there are court transcripts with Signal logs entered as evidence, I consider them non trustworthy, to understate it.
@alexwinter @mekkaokereke @rysiek @tchambers
@lauren I am also not alone in shunning Signal.
Also see:
https://www.jwz.org/blog/2018/08/signal/
https://www.jwz.org/blog/2017/03/signal-leaks-your-phone-number-to-everyone-in-your-contacts/
https://www.jwz.org/blog/2021/04/signal-hops-on-the-dunning-krugerrand-bandwagon/
etc. @alexwinter @mekkaokereke @rysiek @tchambers
Signal
Drew DeVault: I don't trust Signal: I expect a tool which claims to be secure to actually be secure. I don't view "but that makes it harder for the average person" as an acceptable excuse. If Edward Snowden and Bruce Schneier are going to spout the virtues of the app, I expect it to actually be secure when it matters - when vulnerable people using it to encrypt sensitive communications are ...
@lauren The US is of course not immune, it's one of the worst places on Earth for human rights abuses and privacy violations. But two decades ago there were not the preponderance of multiple (some interoperable) encryption tools that exist now. I had Cisco VPN concentrator CD-ROMs which said: "Not for export outside of the USA" and "Made in Mexico" on the same friggin label two decades ago.
@alexwinter @mekkaokereke @rysiek @tchambers
@lauren " pulling out of countries where end-to-end crypto is made illegal" seems to be rather different than, e.g. (now PhD) Niels Provos' efforts to work on OpenSSH by DRIVING ACROSS THE USA BORDER so he was not in violation of international laws while he was a grad student at UMich. Niels Provos did self sacrifice to help all, Signal has not demonstrated anything approaching that, anywhere, ever.
@alexwinter @mekkaokereke @rysiek @tchambers