Things I found interesting in Mandiant's M-Trends 2023 report, a thread. This is their yearly report on cybersecurity.
Direct link to PDF, to avoid the sales lead generator: https://mandiant.widen.net/s/dlzgn6w26n/m-trends-2023
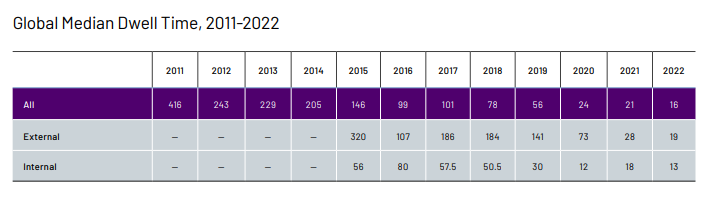
For starters - dwell time - how long orgs take to detect incidents - is at its lowest ever, at 16 days (13 days for internal incidents).
"Improvements in global median dwell time in 2022, regardless of detection source, enabled organizations to respond to incidents faster than ever before."