@nixCraft does this take into account common mitigations like account being disabled after x failures or exponential time back off ?
I’m not arguing for crap passwords, but realistic attack simulations.
@walkerb @nixCraft The methodology section of their page is insufficient. My strong presumption is this is attempting to model the "I got the (salted) hash" threat model, and not the online attack model.
Frankly I don't believe their results given an actually random password. I DO believe it given a human generated password, as the lack of entropy in our brains should be modelable by a similar lack of entropy in a LLM.
The callout here should be "let your password manager do it's thing"
@walkerb @nixCraft That assumes that you can't get the salt when you get the hash ... which for most breaches I'm aware of, seems like a fraught assumption.
(I mean, I guess you *could* store the salt in a cookie on the user's system, and literally not have it otherwise, and just brute-force-it whenever a user logs in from a new system, but ... I've not heard of anyone implementing such a system)
@kilpatds @nixCraft depends on the depth of the compromise.
I typically store salts in a different storage modality to the user accounts. Requiring a different set of credentials and keys to access.
I detest AI sensationalism - if what you're actually telling me is you have a better word list then color me less impressed.
@walkerb @nixCraft https://elk.zone/mastodon.social/@kilpatds/110181481022106276
"A better word list" seems like a reasonable approximation. @kevinbowrin linked to the paper: https://arxiv.org/abs/1709.00440
My quick take is "an AI trained on all cracked passwords was able to generate cracked passwords"... which ... uh ... yes?
Douglas Kilpatrick (@[email protected])
Attached: 1 image Reading the methodology behind https://www.homesecurityheroes.com/ai-password-cracking/ and thinking of this image, for no particular reason.
@walkerb @nixCraft from the page, it seems like this is just a better wordlist based on RockYou.
> The technology was trained using the RockYou dataset, a data group used to train intelligent systems on password analysis. After training, GAN was able to leverage the acquired knowledge to create new sample passwords that follow the neural network distribution.
@DuncanWatson @nixCraft respectfully disagree - if its against has, then a well used salt will move weak passwords further up the table.
So an 8 character password would effectively be a 20+ character password...
This is simply sensationalism.
@walkerb @nixCraft I agree that the chart is too simple. But dealing with salts and other issues is absolutely normal in the cracking world and has been for over 20 years.
An 8 character password though is pretty terrible. Length of your password is your best defense. There is no way I could imagine anyone justifying 8 character passwords in the modern world.
I'm not arguing for bad passwords.
I'm arguing that this is AI sensationalism for what amounts to a better word list...
@walkerb @nixCraft I agree, the AI part of this is 100% BS. Especially since it isn't bringing in any more inputs. Like if you told me you had a system that could target the CEOs passwords based on their profile of said CEO. I would then pay attention. That is very believable without AI.
Heck just building a matrix of your target and recently security breaches will get you a lot of hits.
@DuncanWatson @walkerb the more interesting part is, as usual, not with so much eyecandy so it didn't make it. This goes back to a paper in 2017: https://doi.org/10.48550/arXiv.1709.00440
Brief overview is that it "guesses" by adding typical patterns used for "save passwords", like l33tsp34k, for decades.
Here is a repo putting it to a test https://github.com/brannondorsey/PassGAN
…mebbe that website is even running this in the background 🤷
Bottom line is IMHO that someone got to show their CSS skills here and that's it 🤓
PassGAN: A Deep Learning Approach for Password Guessing
State-of-the-art password guessing tools, such as HashCat and John the Ripper, enable users to check billions of passwords per second against password hashes. In addition to performing straightforward dictionary attacks, these tools can expand password dictionaries using password generation rules, such as concatenation of words (e.g., "password123456") and leet speak (e.g., "password" becomes "p4s5w0rd"). Although these rules work well in practice, expanding them to model further passwords is a laborious task that requires specialized expertise. To address this issue, in this paper we introduce PassGAN, a novel approach that replaces human-generated password rules with theory-grounded machine learning algorithms. Instead of relying on manual password analysis, PassGAN uses a Generative Adversarial Network (GAN) to autonomously learn the distribution of real passwords from actual password leaks, and to generate high-quality password guesses. Our experiments show that this approach is very promising. When we evaluated PassGAN on two large password datasets, we were able to surpass rule-based and state-of-the-art machine learning password guessing tools. However, in contrast with the other tools, PassGAN achieved this result without any a-priori knowledge on passwords or common password structures. Additionally, when we combined the output of PassGAN with the output of HashCat, we were able to match 51%-73% more passwords than with HashCat alone. This is remarkable, because it shows that PassGAN can autonomously extract a considerable number of password properties that current state-of-the art rules do not encode.
PassGAN: A Deep Learning Approach for Password Guessing
State-of-the-art password guessing tools, such as HashCat and John the Ripper, enable users to check billions of passwords per second against password hashes. In addition to performing straightforward dictionary attacks, these tools can expand password dictionaries using password generation rules, such as concatenation of words (e.g., "password123456") and leet speak (e.g., "password" becomes "p4s5w0rd"). Although these rules work well in practice, expanding them to model further passwords is a laborious task that requires specialized expertise. To address this issue, in this paper we introduce PassGAN, a novel approach that replaces human-generated password rules with theory-grounded machine learning algorithms. Instead of relying on manual password analysis, PassGAN uses a Generative Adversarial Network (GAN) to autonomously learn the distribution of real passwords from actual password leaks, and to generate high-quality password guesses. Our experiments show that this approach is very promising. When we evaluated PassGAN on two large password datasets, we were able to surpass rule-based and state-of-the-art machine learning password guessing tools. However, in contrast with the other tools, PassGAN achieved this result without any a-priori knowledge on passwords or common password structures. Additionally, when we combined the output of PassGAN with the output of HashCat, we were able to match 51%-73% more passwords than with HashCat alone. This is remarkable, because it shows that PassGAN can autonomously extract a considerable number of password properties that current state-of-the art rules do not encode.
@nixCraft How is it any different than a regular brute force with a wordlist? do they only generate better wordlists?
Let's say they want to crack my mastodons instance admin password. How is it different then?
@nixCraft
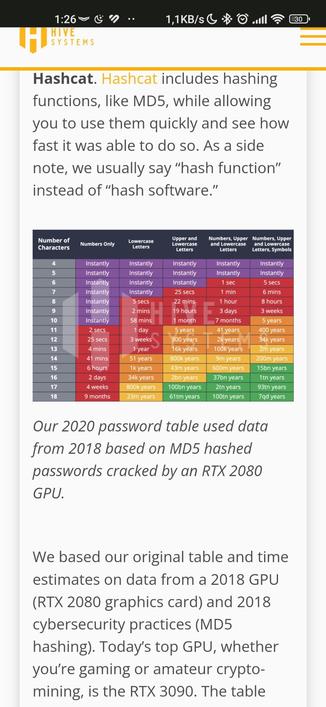
The 17 Upper & Lower Char time is significantly smaller than 16 Char...
The color coding makes that stick out like a sore thumb, it doesn't happen elsewhere on the chart.
Is there an explanation for that?