@LukaszOlejnik Interesting paper. #Threema’s response very much comes across as downplaying:
· Threema does not link to the paper, instead preferring that people build their opinion only from the information Threema provides.
· Threema does not mention the issues being reported to them in October 2022. Neither do they mention when the new Ibex communication protocol was released (November 2022). This way they don’t have to answer the question whether all these issues being addressed in Ibex was a coincidence or the result of responsible disclosure.
· At the same time their blog post suggests that the researchers were investigating an outdated protocol. No, the protocol they investigated was current at the time. It only got replaced after Threema received the reports.
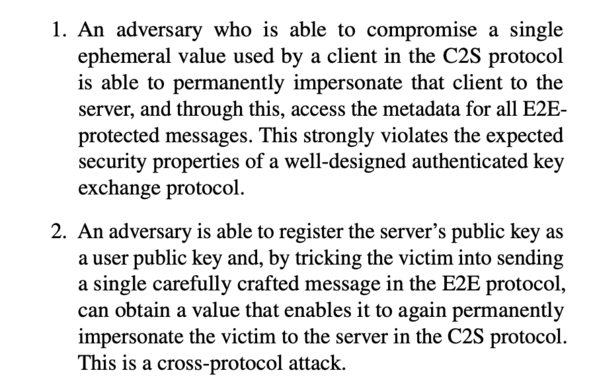
· There is some dismissing of issues as not having real-world impact. This may be the case, yet they are still design flaws even if nobody managed to exploit them (e.g. because other security layers prevented that).
· “Extensive prerequisites” doesn’t necessarily devalue a finding like Threema’s blog post seems to suggest. Exploitation may look implausible now, but with the flaw being out there someone might find easier ways to exploit it.
In the end, I think that the researchers do oversell their achievements. These flaws aren’t nice, but they don’t really compromise the integrity of the protocol either.
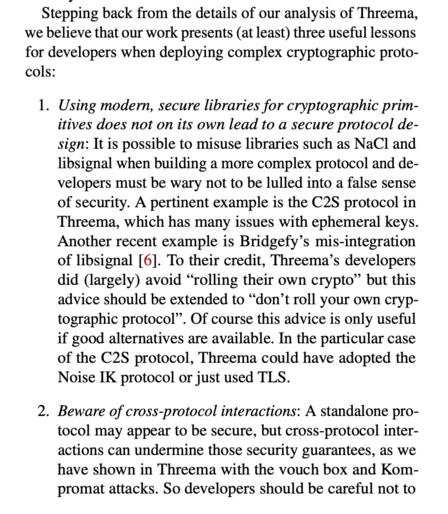
Still, Threema could have handled it better. Being serious about security means not dismissing issues just because these have low impact, are hard to exploit or apply to a protocol that you are in the process of replacing anyway. Each reported issue is a chance for you to learn.