Using apps like LastPass — which require you to upload your passwords and a bunch of other info on all your online accounts — has always been the epitome of stupidity.
@kordinglab
No, with a keylogger they can get your master password, so you're screwed either way.
Also, there's plenty of middle ground between not using a password manager and using a proprietary one that uploads all your passwords to the cloud.
@kordinglab I understand it's very convenient.
But the idea that there is a central service that stores thousands of people's passwords if frankly absurd from a security perspective.
I understand that the passwords are encrypted before they are uploaded, but the attack surface becomes so large that I would never feel safe with such a system.
I store my passwords with the Gnome keyring and Firefox. I also only need to type the master password. But my passwords never leave my machine.
@kordinglab They don't get to my phone. I lose that convenience. There is usually a trade-off between convenience and security, and this is what I choose.
The larger attack surface is a problem because encryption is not fail-safe, and now there is a central point of failure.
Don't underestimate the ability of someone cracking your master password if they have access to the raw ciphertext. See here: https://social.skewed.de/@gsuberland@chaos.social/109559625014104081
Besides, it may not be necessary for attackers to crack your master password. If they can crack one of your hundreds of encrypted passwords — for example because it's a simple password, or has been generated with a known or faulty algorithm, the attacker can go from there.
Graham Sutherland / Polynomial (@[email protected])
if you run into anyone trying to discount the severity of the lastpass breach by saying the master keys are impossible to crack, ask them how lastpass' key derivation works, what a credential stuffing attack is, and how well PBKDF2 scales on GPUs. given the details, it looks like anyone whose data was in the breach and who also reused their master password elsewhere is in imminent danger of having all their passwords compromised, as is anyone who used a relatively common password.
The lack of convenience with passwords _is_ the issue.
Far more breaches have occurred due to password reuse (often associated with credentials stuffing) than from attacks on password managers.
Cloud sync of passwords is a security-convenience trade-off, but for me personally, with it. And at the macro level, likely worth it as well.
2022: A Look Back On A Year Of Mass Exploitation
Researchers at GreyNoise Intelligence have added over 230 tags since January 1, 2022, which include detections for over 160 CVEs. In today’s release of the GreyNoise Intelligence 2022 "Year of Mass Exploits" retrospective report, we showcase four of 2022's most pernicious and pwnable vulnerabilities.
@gdbassett @kordinglab I don't need to tell you that small servers are also less important targets.
If find the “quality of software” argument strange, since it's same for every scenario.
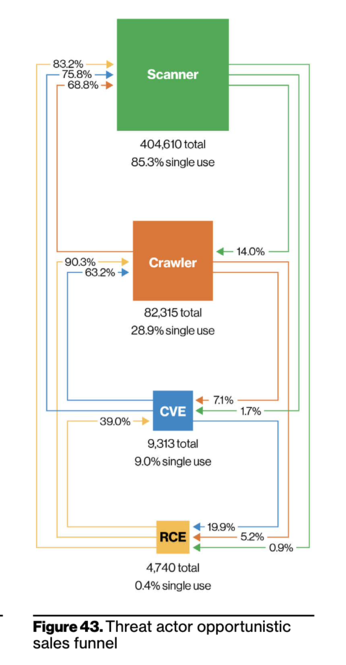
@tiago @kordinglab Attackers tend to be economically driven. A rising issue is to take critical vulnerabilities, automate their exploitation, and then sell the access.
In our 2022 report (page 31, figure 43), from honeypot data, we observed a type of attacker sales funnel from scanning for hosts to executing an exploit.
@tiago @kordinglab Thankfully there isn't a single centralized password manager. There's lastpass, 1Password, bitwarden, the password managers in browsers, in OSs, and many others.
And it's definitely a balance (and one that isn't settled in the security community). For example, a common solution is to use 1password and sync the vault through something like dropbox.
Fernando Montenegro :donor: (@[email protected])
Content warning: long-ish, related to LP disclosure
That's what I lean towards. I need to find a way to support family usage (mobile devices, multiple browsers, ...).