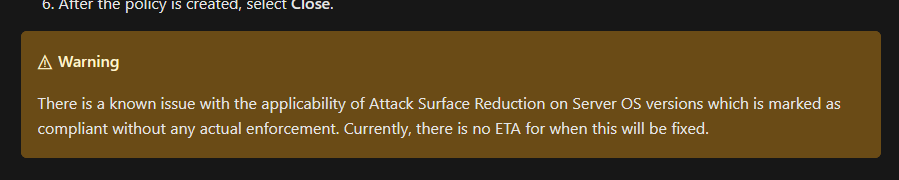
Hahaha. Lost hours to deploy Defender ASR rules + Network protection to Win servers via SCCM. Turns out there's a bug and it won't work. No ETA for a fix. Great.
https://learn.microsoft.com/en-us/microsoft-365/security/defender-endpoint/enable-attack-surface-reduction?view=o365-worldwide#microsoft-endpoint-configuration-manager
https://learn.microsoft.com/en-us/microsoft-365/security/defender-endpoint/enable-attack-surface-reduction?view=o365-worldwide#microsoft-endpoint-configuration-manager