#BHUSA #usesec24 #USENIX2024
Find out more: https://www.usenix.org/system/files/usenixsecurity24-lamster.pdf
#usesec24 #USENIX2024
#BHUSA #usesec24 #USENIX2024
Our #usenix2024 paper "SIMurai: Slicing Through the Complexity of SIM Card Security Research" just went public!
We asked ourselves: What kind of attacks could a hostile SIM launch against your phone?
The second to last trifecta of #HackerSummerCamp, here is the #DCG201 2024 guide for @usenixassociation, @soups & @wootsecurity: https://defcon201.medium.com/hacker-summer-camp-2024-guides-part-sixteen-usenix-security-trifecta-2024-c0e80833eb2d
#usenix #usenix2024 #usenixsecurity #soups #soups2024 #woot #w00t @defcon @philly2600 @bsidesphilly
I had the pleasure to contribute to Lukas Maar's #USENIX2024 paper "SLUBStick".
SLUBStick elevates limited heap vulnerabilities within the #Linux kernel to arbitrary memory read-and-write primitives, leveraging a timing side channel.
Thanks to Lukas Maar, Martin Unterguggenberger, Mathias Oberhuber and Stefan Mangard for this great opportunity!
Congratulations to Lukas Maar for driving the paper to acceptance at USENIX Security!
You can read the full paper here: https://stefangast.eu/papers/slubstick.pdf
#SLUBStick #Kernel #Linux #KernelSecurity #sidechannel #usenixsecurity #usenixsec
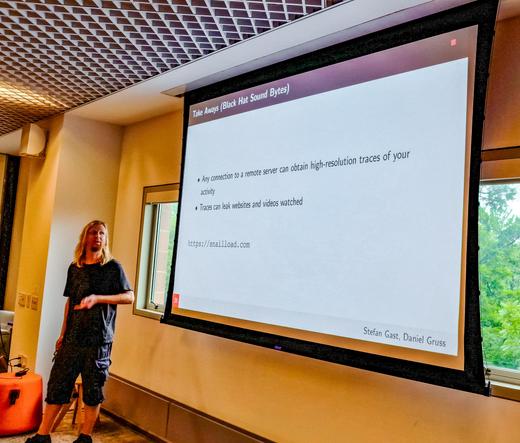
Also looking forward to present #SnailLoad at #USENIX2024.
(3/3)
I had the pleasure to contribute to the #USENIX2024 paper "Divide and Surrender", recovering the full secret key from the reference implementation of the HQC Key Encapsulation Mechanism, exploiting a timing side channel arising from non-constant-time modulo operations.
Thanks to Robin Leander Schröder and Qian Guo for this opportunity and congratulations to Robin Leander Schröder for getting his first paper accepted at USENIX Security!
You can read the full paper here: https://stefangast.eu/papers/divide_and_surrender.pdf
#divideandsurrender #hqc #sidechannel #postquantumcrypto #usenixsecurity