https://youtu.be/3KCyhltnz7w?t=721
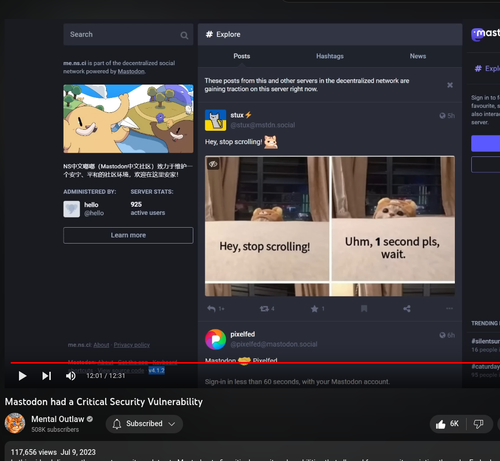
Mastodon had a Critical Security Vulnerability
@monster_mistress are you on this #tootroot fix already? Thanks for all you do! 💙💙💙
tiddy roosevelt (@[email protected])
There are still a whole lot of Mastodon servers that need to install security vital updates in light of the TootRoot vulnerability! If you see any outdated instance where it's: ° Mastodon 4.1.x below 4.1.3 ° Mastodon 4.0.x below 4.0.5 ° Mastodon 3.5.x below 3.5.9 and you have any way of directly contacting the admins, please do. The vulnerability is now widely known about so it's important admins get protected from it. You can find version info on the bottom of the instance about page!
Avec la faille de sécurité TootRoot, un attaquant peut compromettre un serveur Mastodon
With that vulnerability known all about now of Masto's.. the one way there is as a visitor to avoid getting hit by an outdated instance being exploited, is not having JS enabled by default for when browsing untrusted originating instances.
In terms of Masto pre v4, that disables all media and link previews on posts to just be links instead, and post v4, well JS is mandatory since the removal of the static UI.
Masto really should, same for every other fedi software and any web software in general were JS is required, display the current version number of the software, with a link to the source code when being told to enable JS. That would be really valuable information to be able to go off to decide whether to enable JS or not.
As it is right now with much software where JS is mandatory, you're forced to enable JS to see the version. That should change.
Wouldn't change the fact that with pre v4 instances being exploited, that it's not just the previews. The admin account or anything on the instance could be tooting out crap and other things manipulated if it's exploiting having access to the system user Masto runs as.. which for a very bad dangerous install well I bet there have been some with the clever idea to run masto as root. But yea still.. without JS enabled, you're blocking what can and will be the most damaging when browsing an exploited instance.
I run a Mastodon instance on Digital Ocean. Upgrading a 4.0.X instance there was pretty darn easy.