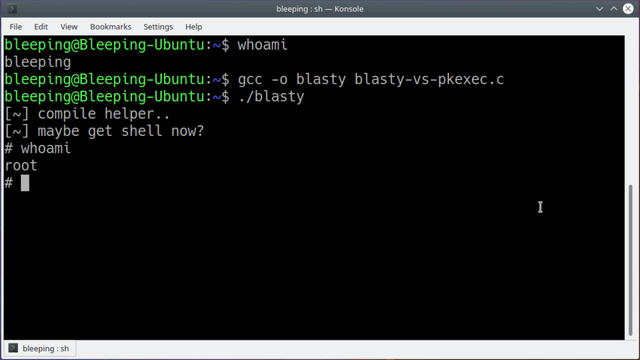
Rooted another OSCP machine this morning. There is no other exploit that has been more widespread and easy to leverage than pwnkit (CVE-2021-4034). I've simply lost count of the the number of machines I've been able to use this on to get root access from a low-privilege account. For people who do this kind of stuff, this post is a cold take, but I just wanted to come here and state the obvious. #OSCP #pwnkit #polkit #CVE-2021-4034 #Linux #pkexec #setuid
From the Ubuntu website: "A local privilege escalation vulnerability was found on polkit’s pkexec utility. The pkexec application is a setuid tool designed to allow unprivileged users to run commands as privileged users according predefined policies. The current version of pkexec doesn’t handle the calling parameters count correctly and ends trying to execute environment variables as commands. An attacker can leverage this by crafting environment variables in such a way it’ll induce pkexec to execute arbitrary code. When successfully executed the attack can cause a local privilege escalation given unprivileged users administrative rights on the target machine."