🚨 NEWS: Ethical Hacking in Italia: metodologia operativa e framework legale per il penetration testing
Ecco i punti chiave in breve:
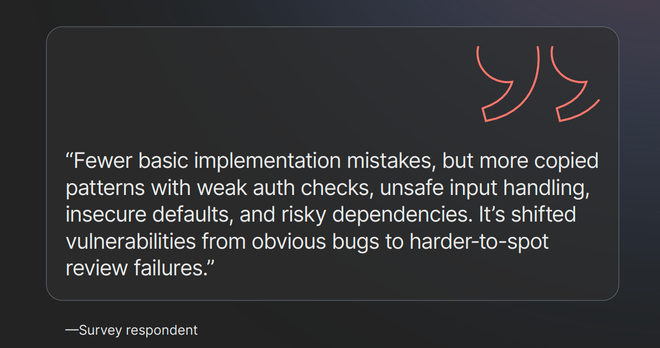
💡 Hai ricevuto l'incarico di testare la sicurezza di un'azienda italiana. Sei sicuro di sapere cosa puoi fare legalmente e cosa no? Un errore di confine tra test autorizzato e violazione di sistema può...
#ethicalHacking #gDPR #meteoraWeb #oWASP #penetrationTesting