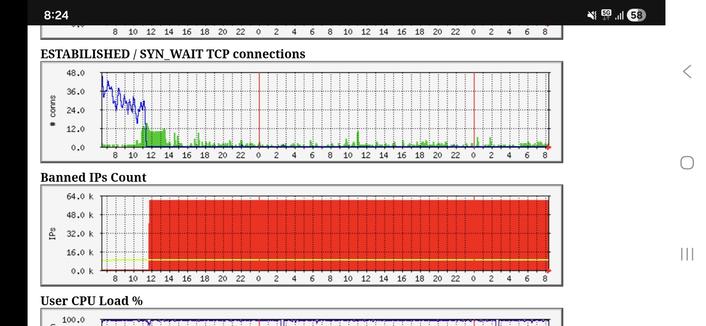
Три слоя защиты сервера: ipset, auto-block и CrowdSec
Ваши логи забиты попытками входа в .env , .git и wp-login.php ? Пока бот стучится в Nginx, ваш сервер уже тратит драгоценные ресурсы. Я решил перенести фильтрацию в ядро Linux и делюсь рабочим кейсом эшелонированной обороны на базе ipset и CrowdSec .
https://habr.com/ru/articles/1019778/
#WAF #ipset #iptables #CrowdSec #Битрикс #защита_сервера #безопасность #Linux #bashскрипты #информационная_безопасность