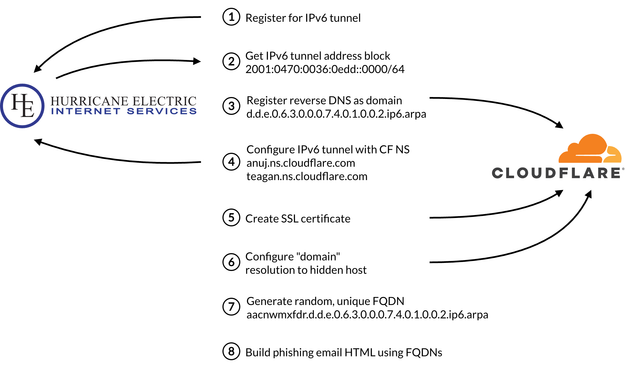
We discovered a phishing actor that is abusing .arpa to host content on domains that should not resolve to an IP address. The actor uses free services to create domain names from reverse DNS strings for IPv6 tunnels that use the .arpa top level domain. These domains are unlikely to be blocked, much less scrutinized, by security systems as they aren’t supposed to be used in URLs. But this actor is doing just that. Every day.
We’ve seen a constant flow of phishing emails using these domains as phishing links since last November. The scam uses a toolkit that has been used since at least 2017. Another campaign using the same toolkit leverage hijacked CNAMEs of well-known government agencies, universities, telecommunication companies, media organizations, and retailers from around the world.
In our latest blog, we explain what these actors are doing and how they are doing it. We even share all the indicators we’ve uncovered.
#dns #threatintel #threatintelligence #cybercrime #cybersecurity #infosec #infoblox #infobloxthreatintel #scam #phishing #hijackedcname