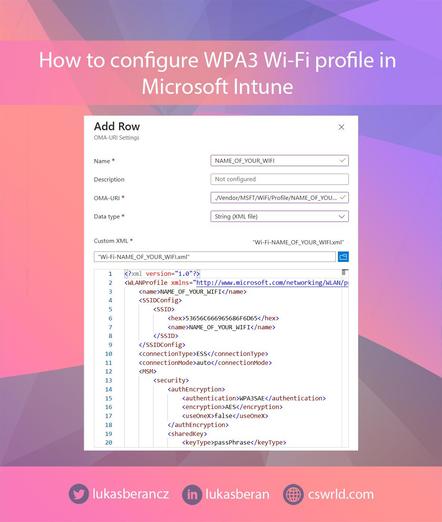
𝐇𝐨𝐰 𝐭𝐨 𝐜𝐫𝐞𝐚𝐭𝐞 𝐚 𝐖𝐏𝐀3 𝐖𝐢-𝐅𝐢 𝐩𝐫𝐨𝐟𝐢𝐥𝐞 𝐟𝐨𝐫 𝐖𝐢𝐧𝐝𝐨𝐰𝐬 𝐢𝐧 𝐌𝐢𝐜𝐫𝐨𝐬𝐨𝐟𝐭 𝐈𝐧𝐭𝐮𝐧𝐞
Microsoft Intune still cannot natively create a Wi-Fi profile with WPA3-Personal security at this time. Within the configuration templates, there is only Wi-Fi with WPA/WPA2 security, but WPA3 is missing.
If you have a Wi-Fi where WPA3 is enforced without hybrid mode with WPA2, then if you create a profile as WPA2, the device will not connect to it. So, if you have WPA3 enforced, you need to configure Wi-Fi using a custom profile and OMA-URI.
https://www.cswrld.com/2026/03/how-to-create-a-wpa3-wi-fi-profile-for-windows-in-microsoft-intune/