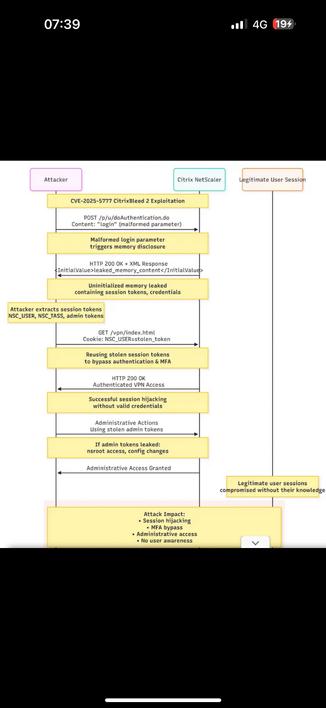
🚨 Over 3,300 Citrix NetScaler devices remain unpatched against the critical #CitrixBleed2 vulnerability (CVE-2025-5777), risking session hijacks & MFA bypass! Attackers can steal session tokens remotely. Patch now to avoid data breaches and network risks! 🔐🛡️ #newz
Details: https://www.bleepingcomputer.com/news/security/over-3-000-netscaler-devices-left-unpatched-against-actively-exploited-citrixbleed-2-flaw/ #Cybersecurity #InfoSec #NetScaler
Citrix users, your NetScaler devices might be leaving your data wide open. Over 3,300 systems are still unpatched, letting hackers bypass authentication like a "master key." Is your network at risk? Dive into the details and protect your assets now.
https://thedefendopsdiaries.com/understanding-and-mitigating-the-citrixbleed-2-vulnerability/
#citrixbleed2
#netscaler
#cybersecurity
#vulnerability
#patchmanagement
The Dutch Public Prosecution Service Citrix Netscaler incident is rumbling on. They are working on service recovery.
https://www.databreachtoday.com/dutch-prosecutors-recover-from-suspected-russian-hack-a-29129
Emerging situation to be aware of - some of the #CitrixBleed2 session hijacking victims are also victims of webshell implants via a different vuln, CVE-2025-6543.
Script to check for Netscaler implants: https://github.com/NCSC-NL/citrix-2025/blob/main/TLPCLEAR_check_script_cve-2025-6543-v1.6.sh
 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉