Video: https://www.youtube.com/watch?v=hmzKun6eFh8
#penesting #redteaming #bypassav #evasion #inmemory #redteam #pentest
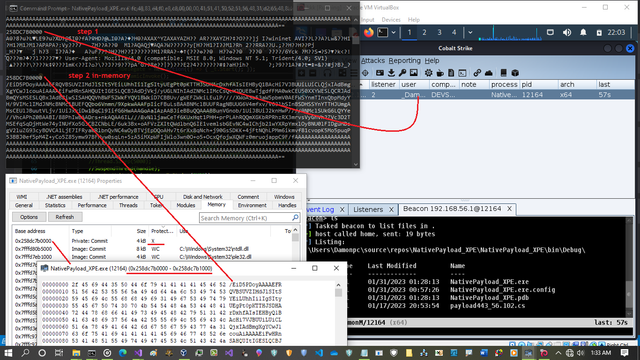
Simple Trick:Code behavior detected by Anti-virus and Bypassing Some AVs via Sleep,timer trick in C#
KASPERSKY #Bypassed and ...
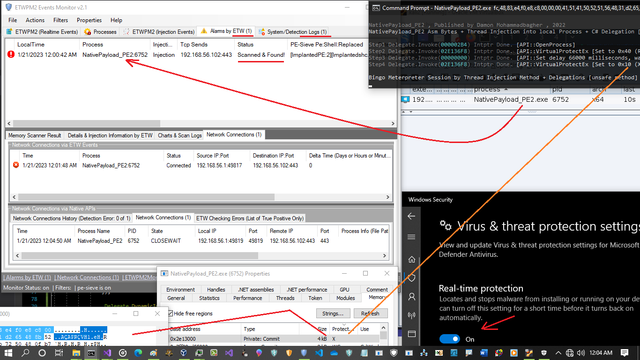
NativePayload_PE1/PE2 also some New code Which Callback Function API integrated to Delegation Method [Technique D] & Bypassing some AVs, source code available in my Github [https://github.com/DamonMohammadbagher/NativePayload_PE1] but those two new Codes "NativePayload_AsynASM.cs + NativePayload_ASM3.cs" will share in the future but you can see source code in Video ;D
#penesting #redteaming #bypassav #evasion #inmemory #redteam #pentest
GitHub - DamonMohammadbagher/NativePayload_PE1: NativePayload_PE1/PE2 , Injecting Meterpreter Payload bytes into local Process via Delegation Technique + in-memory with delay Changing RWX to X or RX or (both) [Bypassing AVs]
NativePayload_PE1/PE2 , Injecting Meterpreter Payload bytes into local Process via Delegation Technique + in-memory with delay Changing RWX to X or RX or (both) [Bypassing AVs] - GitHub - DamonMoha...
with Native API you can change #Process Memory very simple and i tested simple c# code to Convert payload #inmemory before running payload also after running payload with delay so In-memory every 60 secs only once RAW payload will run in memory and this code still needs to test but i did not have any error in Server-side or client-side and #Cobaltstrike commands worked very well but still needs to work on this code (this code just was for test),
btw code was not Detected by Kaspersky so i can say KASPERSKY Bypassed again ;D
anyway #Encrypting or #obfuscating in-memory can help you sometimes ;)
#penesting #redteaming #bypassav #evasion #inmemory #redteam #pentest
Video: Kaspersky v21.3 vs New C# Code and Bypassed very well
some real sources: some engineers in some Anti-virus Companies say "COME-ON" ;D etc.
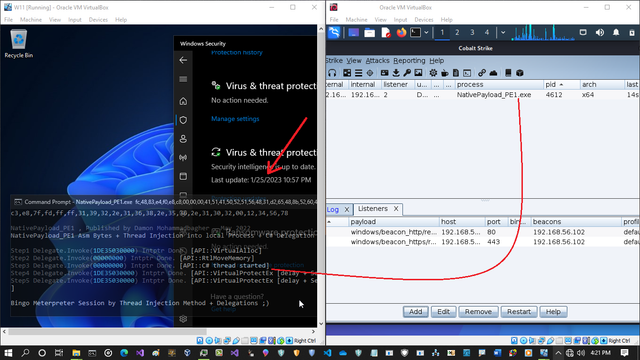
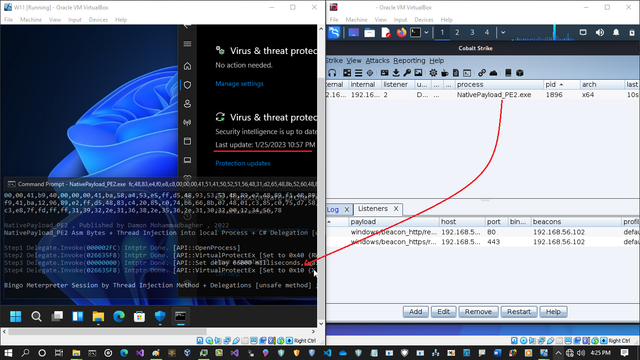
Simple Technique to Load Assembly/Bytes into local process (in-memory) via C# Delegation + Native APIs and Bypassing Anti-viruses ;), some part of code changed via [D]elegate Techniques which i called [Technique ;D] to change some behavior of code (also change source code) and ...
https://www.youtube.com/watch?v=sqyKqiU1lsE
Source code => https://lnkd.in/eZEEhfDY
article => https://lnkd.in/e4PPJe7R
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive #kaspersky #redteam #pentest
Kaspersky Bypassed via New C# Code to injecting code into local process
Two C# Methods and test on Win 11 [v22H2] with last updates.
Simple #Technique to Load Assembly/Bytes into local process (#inmemory) via C# #Delegation + #Native #APIs and #Bypassing Anti-viruses ;), some part of code changed via [D]elegate Techniques which i called [Technique ;D] to change some #behavior of code (also change source code) and Method is not really new but C# code a little bit is ;D [since 2022 i used this], changing RWX to X and after 2 min to RX by "NativePayload_PE1.cs" or changing RWX to X only by "NativePayload_PE2.cs"
and
some anti-virus companies say "COME-ON", like Kaspersky ;D
note: as #pentester you really need to change your own codes sometimes very fast , these codes changed and again worked very well and as #securityresearcher this is really fun to find out new method/codes to bypass AVs always ;D
article => https://lnkd.in/e4PPJe7R
source code => https://lnkd.in/eZEEhfDY
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive
2 Simple C# Techniques for Bypassing Anti-virus
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive 2 Simple C# Techniques for Bypassing Anti-virus in this article i want to talk about two C# Techniques which was tested by me on WIN10 for bypassing Anti-virus so both of them is about using "VirtualProtectE
Two C# Methods vs "Kaspersky cloud security v21.3"
now testing Kaspersky with last update 22/1/2023 and bypassed very well
Simple #Technique to Load Assembly/Bytes into local process (#inmemory) via C# #Delegation + #Native #APIs and #Bypassing Anti-viruses ;), some part of code changed via [D]elegate Techniques which i called [Technique ;D] to change some #behavior of code (also change source code) and Method is not really new but C# code a little bit is ;D [since 2022 i used this], changing RWX to X and after 2 min to RX by "NativePayload_PE1.cs" or changing RWX to X only by "NativePayload_PE2.cs"
and
some anti-virus companies says "COME-ON", like Kaspersky ;D
note: as #pentester you really need to change your own codes sometimes very fast , these codes changed and again worked very well and as #securityresearcher this is really fun to find out new method/codes to bypass AVs always ;D
article => https://www.linkedin.com/pulse/2-simple-c-techniques-bypassing-anti-virus-damon-mohammadbagher/
source code => https://github.com/DamonMohammadbagher/NativePayload_PE1
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive #kaspersky
2 Simple C# Techniques for Bypassing Anti-virus
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive 2 Simple C# Techniques for Bypassing Anti-virus in this article i want to talk about two C# Techniques which was tested by me on WIN10 for bypassing Anti-virus so both of them is about using "VirtualProtectE
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive
source code => https://github.com/DamonMohammadbagher/NativePayload_PE1
GitHub - DamonMohammadbagher/NativePayload_PE1: NativePayload_PE1/PE2 , Injecting Meterpreter Payload bytes into local Process via Delegation Technique + in-memory with delay Changing RWX to X or RX or (both) [Bypassing AVs]
NativePayload_PE1/PE2 , Injecting Meterpreter Payload bytes into local Process via Delegation Technique + in-memory with delay Changing RWX to X or RX or (both) [Bypassing AVs] - GitHub - DamonMoha...
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive
https://www.linkedin.com/pulse/2-simple-c-techniques-bypassing-anti-virus-damon-mohammadbagher/
2 Simple C# Techniques for Bypassing Anti-virus
#bypass #bypassav #redteaming #pentesting #blueteaming #csharp #offensivesecurity #offensive 2 Simple C# Techniques for Bypassing Anti-virus in this article i want to talk about two C# Techniques which was tested by me on WIN10 for bypassing Anti-virus so both of them is about using "VirtualProtectE