The Allure of Go’s Cross-Platform Capability: A Gateway for Threat Actors to Mac and Linux
Anmol Maurya, Staff Malware Reverse Engineer at Palo Alto Networks, examines how threat actors use Go to target Mac and Linux systems and what makes detection and analysis so challenging. #BSidesNYC
Contribute to Learn: Building DFIR Expertise Through Open Source
Christopher Eng, Independent Digital Forensic Researcher and CIO, shares how contributing to open-source DFIR tools like KAPE and Velociraptor can accelerate hands-on learning and community growth. #BSidesNYC
Inside Ransomware: Facts and Findings from the BlackBasta and LockBit Leaks
Cory Wolff, Director of Offensive Security at risk3sixty, breaks down leaked data from major ransomware groups to reveal how affiliates collaborate, develop payloads, and profit. #BSidesNYC
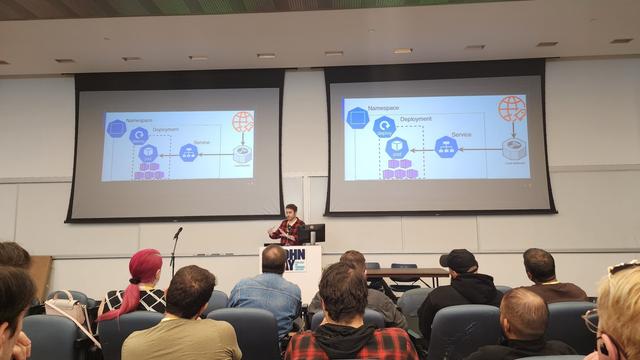
Interactive Networking Fingerprinting Walkthrough
Vlad Iliushin, Cybersecurity Expert at ELLIO and President of AMTSO, leads a hands-on workshop on modern passive fingerprinting techniques like JA3, JA4, p0f, and MuonFP. #BSidesNYC
Rebooting the Cyber Arsenal of Democracy
Eric Foster, CEO of TENEX.ai, shares hard-earned lessons from building and exiting multiple security companies and what it takes to launch and scale a cybersecurity startup in 2025. #BSidesNYC
P0LR Espresso: Pulling Shots of Cloud Live Response & Advanced Analysis
Art Ukshini, Threat Researcher at Permiso Security, presents P0LR Espresso, a tool built to cut through noisy cloud logs, detect threats in real time, and speed up incident response. #BSidesNYC
Bleon Proko, Security Engineer, shows how attackers can use logs to perform enumeration, run C2 channels, and exfiltrate data through cloud infrastructure. #BSidesNYC
The History of Malware: From Floppies to Droppers
Eliad Kimhy, Senior Security Researcher at Acronis, traces the evolution of malware from its early floppy disk days to modern ransomware, showing what has changed and what has stayed the same. #BSidesNYC
Atomic Red Team 101
Gerard Johansen from Red Canary and Ryan Lanciali lead a hands-on workshop on using Atomic Red Team to emulate threats, validate defenses, and strengthen detection and response. #BSidesNYC