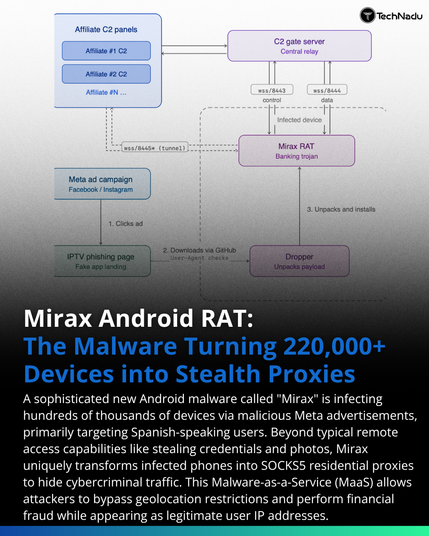
TCLBanker is targeting Android users with banking trojan capabilities - stealing credentials, intercepting messages, and abusing trust at scale. Mobile is still prime territory. 📱💸 #BankingTrojan #AndroidSecurity
https://thehackernews.com/2026/05/tclbanker-banking-trojan-targets.html