Alert fatigue leads to missed signals. Correlation, prioritization, and automated triage are essential to reduce noise and protect analyst focus.
SOC alert fatigue continues to grow.
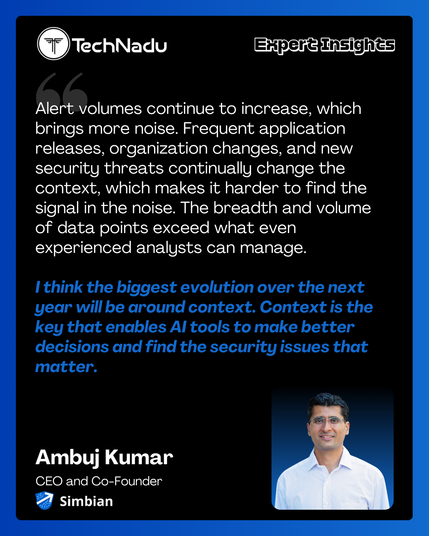
Ambuj Kumar, CEO and Co-Founder of Simbian, explains:
“Alert fatigue is a very real problem. Most enterprise SOC teams routinely don’t have time to review 40% or more of the security alerts that they receive.”
AI-driven automation may help reduce investigation workload.
Read the interview:
https://www.technadu.com/threats-redefine-security-context-ai-ready-operations-will-define-next-gen-soc-ai/623296/
If your alerts fire every day, they’re burnt toast 🍞🚨
Good alerts are rare, actionable, and tied to real user impact.
#SRE #AlertFatigue #OnCall
https://webdad.eu/2026/03/12/%f0%9f%9a%a8-alerts-are-smoke-alarms-not-screaming-toddlers/

🚨 Alerts Are Smoke Alarms, Not Screaming Toddlers - WebDaD - Web Development and Design
Alert fatigue makes on-call miserable and dangerous. Learn why alerts should be rare, actionable, and tied to real user impact—using the simple metaphor of home smoke detectors and burnt toast.
Security teams are drowning in alerts, and AI might not be the answer everyone thinks it is.
In this episode, Erik Bloch, VP of Security at Illumio, breaks down the math on why AI-powered alert triage may be financially unfeasible for most organizations. With 85 to 90 percent of alerts being non-malicious, security teams are still sorting through massive volumes of noise to find the real threats.
Many vendors are betting that AI will solve this problem by triaging alerts at scale. But the reality?
Processing a thousand alerts per day over the course of a year can cost millions of dollars in compute time for LLMs. For most companies outside of Google or major financial institutions, that budget simply doesn't exist.
Erik's take is different: push the problem back to the vendors.
The tools generating 80 to 90 percent garbage alerts are the ones organizations pay millions of dollars per year for. Rather than adding another expensive layer on top to filter the noise, vendors should be delivering higher fidelity alerts from the start.
As a defender, the goal is finding high fidelity alerts that can be actioned. If vendors filtered better on their end, security teams could focus on catching bad guys instead of triaging false positives.
Full episode: https://www.youtube.com/watch?v=BTzrk8h52xk
#cybersecurity #AI #SOC #alertfatigue #infosec #securityoperations #podcast
It's inevitable. As time goes on and needs evolve, you might have to break up with your open-source #SIEM. 😭 We know. It's hard to say "goodbye" to 🆓. 👋 But, as your org grows, it incorporates more business-enabling technologies which lead to new #security risk management tools. This means more logs, impacting performance during high-traffic hours and disrupting the open-source SIEM’s ability to ingest logs. 😱 You need more power.
Is it time for you to upgrade? These 5 signs can help you figure it out:
⬆️ Is your tech stack growing?
📈 Are you scaling your business operations?
↔️ Do you have an expanding attack surface?
😩 Are you experiencing increased alert fatigue?
☑️ Do you have increased compliance needs?
Need help answering these important questions? Read on.👇
https://graylog.org/post/5-signs-youve-outgrown-your-open-source-siem/ #CyberSecurity #InfoSec #AlertFatigue
Cảnh báo: Bạn cần một ngân sách! Cảnh báo làm tăng tải công việc, gây mệt mỏi. Giải pháp: lập ngân sách cho cảnh báo. #AlertFatigue #CảnhBáo #NgânSách #DevOps #LậpTrình #QuảnLýCảnhBáo
https://www.reddit.com/r/programming/comments/1p4uvhw/alerts_you_need_a_budget/
Choosing a #SIEM doesn’t have to mean trade-offs! 🔄 Watch this video and learn how you can get fast detection, predictable costs, and analyst-friendly workflows — without the compromises that hold legacy platforms back. 🙌
Legacy ingest-based SIEMs force #security teams to pick between visibility, cost, and analyst efficiency. But there's a different model that offers flat, transparent pricing, license-free data lake storage, and flexible deployment options — running natively on #AWS.
With this model you can:
✅ Retain all logs without breaking the budget using tiered routing and AWS-backed storage
✅ Cut alert fatigue with campaign-based threat correlation mapped to MITRE ATT&CK
✅ Reduce triage from 20 minutes to 2 minutes with context-aware investigations
✅ Streamline compliance with built-in audit trails, automated reports, and long-term searchable archives
✅ Scale effortlessly with search performance tested at 100+ TB/day
Whether you’re a SOC lead, a #CISO, or a team struggling with AWS log onboarding — see how you can get complete visibility, smarter detection, and cost control in this "Hot 10 Minute Take" with Seth Goldhammer.👇
https://graylog.org/resources/graylog-siem-on-aws/ #CyberSecurity #CISOs #AlertFatigue
Alert fatigue is now responsible for more than half of all #cybersecurity breaches! 😴😱 Why? 🤔
Some reasons are...👇
1️⃣ Attackers are using more subtle methods
2️⃣ Today attackers stretch campaigns out over weeks & blend in to avoid triggering alarms
3️⃣ #Security systems are outdated
4️⃣ Threat notifications are not always helpful & often overwhelm teams
But, don't fret. Campaign-centric detection can help! 🙌 It enables teams to link related activities into broader threat campaigns, creates precise triggers based on individual or aggregated event conditions, and helps eliminate false positives to enhance visibility into genuinely suspicious activity. 👀
💡 Learn more about campaign-centric detection, in this article by #Graylog's Ross Brewer for Resilience Forward: https://resilienceforward.com/how-campaign-centric-detection-can-address-alert-fatigue/ #alertfatigue