Silver Fox lancia ABCDoor: spear phishing con loader Rust personalizzato contro India e Russia, nuova backdoor Python in campo
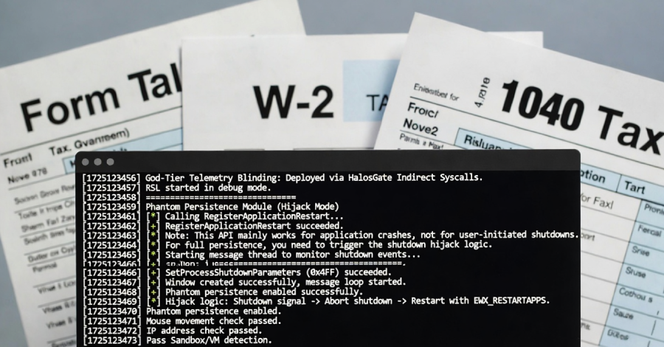
Il gruppo APT cinese Silver Fox ha condotto campagne di spear phishing a tema fiscale contro organizzazioni in India e Russia, distribuendo il backdoor ValleyRAT affiancato da un nuovo payload Python inedito denominato ABCDoor. Kaspersky ha documentato il malware e le tecniche di evasione del loader RustSL, incluso il geofencing per paese e la persistenza tramite Phantom Persistence.📰 Fake LINE Messenger Installer Spreads ValleyRAT Malware
A fake LINE messenger installer is being used to spread ValleyRAT malware. The campaign, linked to the Silver Fox APT, targets Chinese-speaking users for credential theft. 🦊 #Malware #ValleyRAT #CyberSecurity
#ValleyRAT
https://www.cybereason.com/blog/fake-installer-valleyrat
Some fresh (2025-12-18) #silverfox #valleyrat
https://app.any.run/tasks/5f8778b4-7a5a-42fc-b814-4951c356c274
#CheckPoint Research exposed #ValleyRAT’s modular system, including a kernel-mode #rootkit that can remain loadable on fully updated #Windows 11 despite built-in protections. The research linked leaked builder artifacts to plugins and identified about 6,000 samples, with roughly 85 percent emerging in the last six months after the builder’s public release.
https://research.checkpoint.com/2025/cracking-valleyrat-from-builder-secrets-to-kernel-rootkits/
Cracking ValleyRAT: From Builder Secrets to Kernel Rootkits - Check Point Research
Highlights: Introduction Throughout 2025, we conducted and published several reports related to our research on the Silver Fox APT. In some of them (for example, here), the threat actor delivered the well-known ValleyRAT backdoor, also referred to as Winos or Winos4.0, as the final stage. Since this malware family is widely used, modular, and often associated with Chinese threat actors […]
New analysis reveals a Silver Fox operation using a fake Microsoft Teams installer to deploy ValleyRAT in attacks targeting China-based users.
The campaign mixes SEO poisoning, Cyrillic false-flag elements, DLL injection, and BYOVD techniques - making detection and attribution more challenging.
Researchers also note a secondary chain using a trojanized Telegram installer.
What’s your perspective on increased abuse of trusted-app installers in malware campaigns?
Source: https://thehackernews.com/2025/12/silver-fox-uses-fake-microsoft-teams.html
💬 Join the discussion
👍 Boost & follow for more threat intelligence
#CyberSecurity #ThreatIntel #ValleyRAT #SilverFox #InfoSec #MalwareResearch #SecurityOps #CyberThreats
Mentioned Malware Families: ValleyRAT, PureRAT
Aliases for ValleyRAT: win.valley_rat, Winos
Malpedia link for ValleyRAT: https://malpedia.caad.fkie.fraunhofer.de/details/win.valley_rat
Aliases for PureRAT: win.pure_rat, PureHVNC, ResolverRAT
Malpedia link for PureRAT: https://malpedia.caad.fkie.fraunhofer.de/details/win.pure_rat
Aliases provided by Malpedia.
Mentioned Malware Families: ValleyRAT, PureRAT
Aliases for ValleyRAT: win.valley_rat, Winos
Malpedia link for ValleyRAT: https://malpedia.caad.fkie.fraunhofer.de/details/win.valley_rat
Aliases for PureRAT: win.pure_rat, PureHVNC, ResolverRAT
Malpedia link for PureRAT: https://malpedia.caad.fkie.fraunhofer.de/details/win.pure_rat
Aliases provided by Malpedia.
Mentioned Malware Families: ValleyRAT, PureRAT
Aliases for ValleyRAT: win.valley_rat, Winos
Malpedia link for ValleyRAT: https://malpedia.caad.fkie.fraunhofer.de/details/win.valley_rat
Aliases for PureRAT: win.pure_rat, PureHVNC, ResolverRAT
Malpedia link for PureRAT: https://malpedia.caad.fkie.fraunhofer.de/details/win.pure_rat
Aliases provided by Malpedia.
RE: https://infosec.exchange/@VirusBulletin/115660902138702248
How is this #ValleyRAT? It looks, swims and quacks like #PureRAT.
Here are some typical PureRAT indicators: .NET malware
.NET malware
🔑 TLS version is 1.0
JA3 fc54e0d16d9764783542f0146a98b300 / 07af4aa9e4d215a5ee63f9a0a277fbe3
JA4 t10i070500_c50f5591e341_950472255fe9 / t10i060500_4dc025c38c38_950472255fe9
JA3S b74704234e6128f33bff9865696e31b3
📝 X.509 cert expires 9999-12-31 23:59:59 UTC
📡 C2 often runs on TCP 56001
All of them match on the sample analyzed in Trend's report