The #Gentlemen #ransomware now uses #SystemBC for bot-powered attacks
#TheGentlemen #SystemBC
https://research.checkpoint.com/2026/dfir-report-the-gentlemen/

DFIR Report – The Gentlemen & SystemBC: A Sneak Peek Behind the Proxy - Check Point Research
Key Points The Gentlemen RaaS The Gentlemen ransomware‑as‑a‑service (RaaS) operation is a relatively new group that emerged around mid‑2025. The operators advertise their services across multiple underground forums, promoting their ransomware platform and inviting penetration testers (and other technically skilled actors) to join as affiliates. The RaaS provides affiliates with multi‑OS lockers for Windows, Linux, […]
📰 Gentlemen RaaS Expands with SystemBC Botnet for Covert Attacks
Gentlemen RaaS is upgrading its toolkit, using the SystemBC botnet for covert SOCKS5 proxying. The combo enables stealthy C2 and payload delivery for attacks on Windows, Linux, and ESXi. 💣 #Ransomware #SystemBC #Gentlemen #CyberSecurity
Gentlemen Ransomware Spreads Rapidly Through Affiliate Network
Gentlemen Ransomware is spreading rapidly through its affiliate network, fueling a surge in multi-platform attacks and infections linked to the malicious tool SystemBC. This ransomware-as-a-service operation is making it alarmingly easy for cybercriminals to join the fray and wreak havoc.
#Ransomware #GentlemenRansomware #Ransomwareasaservice #AffiliateNetwork #Systembc
Gentlemen Ransomware Gang Taps SystemBC for Botnet Attacks
Imagine your business's infrastructure being hijacked and turned into a fleet of malicious proxies - it's a harsh reality that's now hitting home for over 1,570 corporate victims who've fallen prey to the Gentlemen ransomware gang's SystemBC botnet attacks. Their compromised systems are being used to run proxy services for…
#GentlemenRansomware #Systembc #BotnetAttacks #RansomwareOperations #MalwareOperations
#Mora_001 #Matanbuchus #SystemBC
https://fortgale.com/blog/defence/operation-storming-tide/
Operation Storming Tide: A massive multi-stage intrusion campaign
In February 2026, the Fortgale Incident Response team investigated a multi-stage intrusion attributed to Mora_001, a Russian-origin threat actor exploiting Fortinet vulnerabilities. The campaign, internally dubbed "FortiSync Quasar," revealed an evolution from ransomware operations to strategic espionage, deploying Matanbuchus 3.0, Astarion RAT, and SystemBC. Rapid containment prevented any data exfiltration.
#SystemBC
https://www.silentpush.com/blog/systembc/
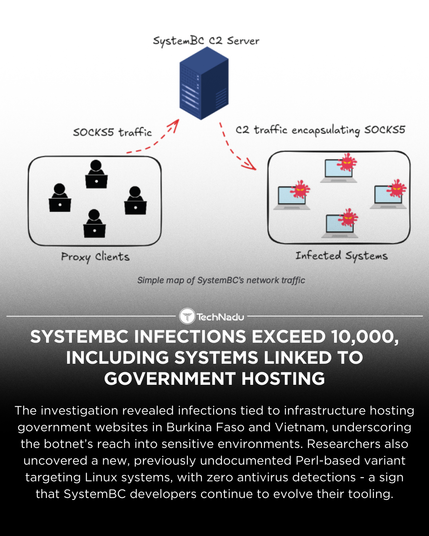
SystemBC infections now exceed 10,000 IPs globally, including systems linked to government hosting.
Silent Push also uncovered a stealthy Linux-targeting Perl variant with zero AV detections.
Thoughts?
#ThreatIntel #Malware #SystemBC #Ransomware
#SystemBC #REMProxy
https://blog.lumen.com/systembc-bringing-the-noise/
A single infected VPS is now pumping out 16GB of proxy traffic a day—turning servers into a cybercrime highway. How is SystemBC reshaping the threat landscape? Read on to uncover the full story.
#systembc
#malware
#vpssecurity
#botnet
#cybercrime
#proxy
#infosec
#threatintelligence
#cybersecurity