#Mora_001 #Matanbuchus #SystemBC
https://fortgale.com/blog/defence/operation-storming-tide/
Operation Storming Tide: A massive multi-stage intrusion campaign
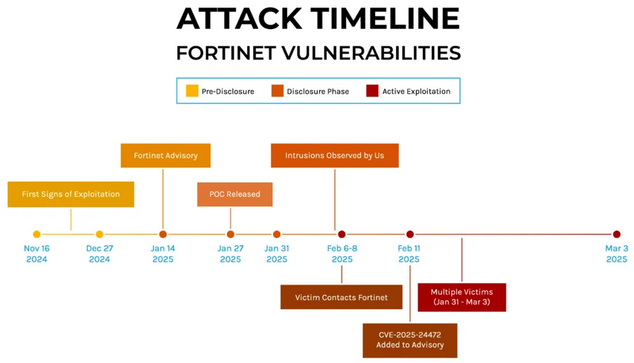
In February 2026, the Fortgale Incident Response team investigated a multi-stage intrusion attributed to Mora_001, a Russian-origin threat actor exploiting Fortinet vulnerabilities. The campaign, internally dubbed "FortiSync Quasar," revealed an evolution from ransomware operations to strategic espionage, deploying Matanbuchus 3.0, Astarion RAT, and SystemBC. Rapid containment prevented any data exfiltration.