🔐 Modern Password Security Threats: Protecting Your Digital Identity 🕵️♀️ 🛡️ 🚨
Cybercriminals use sneaky techniques to crack passwords and gain access to accounts. Here are the most common attacks:
⚒️ Brute Force – Tries every possible password
📖 Dictionary Attack – Uses common words & phrases
🌈 Rainbow Table – Cracks password hashes
👀 Shoulder Surfing – Spies on you while typing
⌨️ Keylogging – Records everything you type
🎯 Password Spraying – Tests common passwords on many accounts
🎭 Social Engineering – Tricks you into revealing passwords
🎣 Phishing – Fake emails & websites steal your login
🎟️ Credential Stuffing – Uses leaked passwords from breaches
🕵️ Man-in-the-Middle – Intercepts data over networks
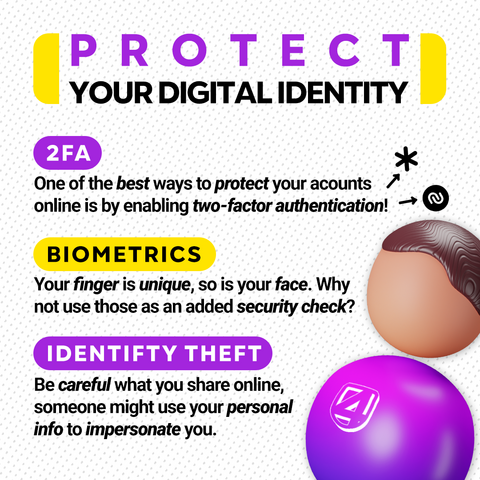
🛡️ Stay Safe! Use strong, unique passwords, enable 2FA, and beware of phishing scams.
Which attack surprised you the most? Let’s discuss in the comments! ⬇️
⚠️ This content is shared strictly for educational and informational purposes only. 📚 All information is provided to help individuals and organizations better protect themselves against security threats. 🔒 The techniques discussed are presented solely to improve awareness and defensive measures, not to facilitate any unauthorized access. ✅
#PasswordSecurity #CyberSecurity #DataProtection #SecureAuthentication #IdentityProtection #InfoSec #PhishingAwareness #CyberDefense #MFA #DigitalSafety