Privacy-preserving tech is accelerating — and OHTTP is quickly becoming core infrastructure.
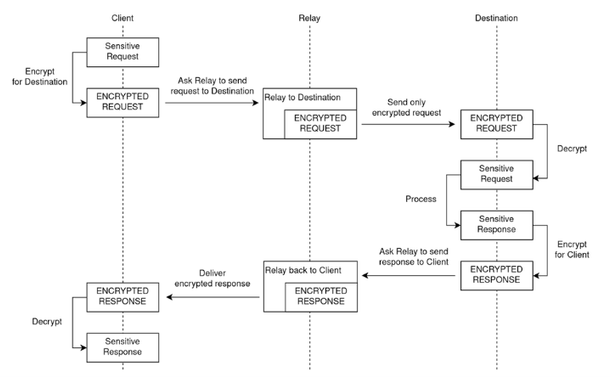
Our partners at Confident (@confidentsecurity) shared an excellent overview of how OHTTP enables anonymous requests across the internet, with adoption from Apple, Google, Mozilla, Meta, and others.
Fastly is proud to be one of the primary OHTTP relay providers, handling tens of millions of requests with low latency and privacy at scale.