----------------
🔍 Threat Intelligence
===================
Overview
IBM X-Force observed Hive0163 deploying a PowerShell backdoor called Slopoly during a ransomware intrusion in early 2026. Researchers characterize Slopoly as AI-assisted or likely LLM-generated based on its structure and extensive commented code. The actor used Slopoly to maintain persistent access for over a week while deploying additional tooling and final ransomware payloads.
Technical findings
• Slopoly: A PowerShell-based C2 client that collects system data, sends heartbeat beacons to a remote server, executes commands via cmd.exe, and establishes persistence through a scheduled task. The code comments and structure strongly suggest AI assistance in development.
• NodeSnake: Identified as the first-stage component in a larger C2 framework used by Hive0163; observed across multiple languages and platforms (PowerShell, PHP, C/C++, Java, JavaScript) and used to download follow-on payloads.
• Windows Interlock ransomware: A 64-bit PE deployed via the JunkFiction loader, supporting arguments for directory/file targeting, self-deletion, scheduled task execution, file release, and external session key storage. Encryption uses per-file AES-GCM with RSA-protected session keys and leaves FIRST_READ_ME.txt as the ransom note. The ransomware leverages the Restart Manager API to stop processes and uses an embedded DLL invoked via rundll32.exe for self-deletion.
• Ancillary tools: Observed use of AzCopy and Advanced IP Scanner to expand access and perform lateral movement.
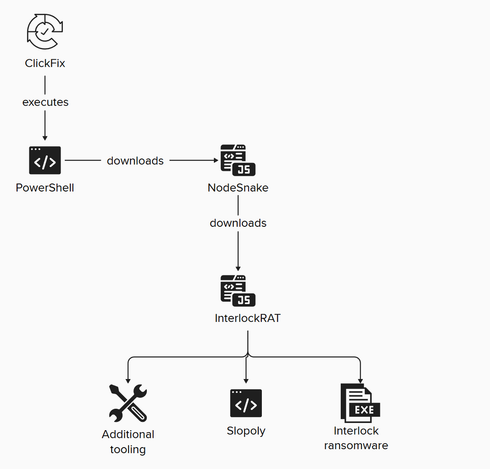
Observed intrusion chain
• 🎣 Initial Access: ClickFix malvertising or broker-assisted access (TA569, TAG-124) that led to a malicious PowerShell command execution.
• 📦 Download: NodeSnake and additional payloads fetched to the compromised host.
• ⚙️ Execution: PowerShell script execution of NodeSnake and loaders such as JunkFiction.
• 🛡️ Persistence: Deployment of Slopoly as a scheduled task providing ongoing C2 heartbeats and remote command execution.
• 🦠 Ransomware Deployment: Final payloads including InterlockRAT capabilities and Windows Interlock ransomware encryption routines.
Conclusions reported
IBM X-Force frames this activity as an example of how advanced LLMs lower the bar for malware development and enable rapid creation of operational tools. The report highlights acceleration of adversarial AI use and anticipates more agentic or AI-integrated malware in future campaigns.
🔹 Slopoly #Hive0163 #InterlockRAT #NodeSnake #WindowsInterlock
🔗 Source: https://securityaffairs.com/189378/malware/ai-assisted-slopoly-malware-powers-hive0163s-ransomware-campaigns.html