#OT #Advisory VDE-2026-042
CODESYS Modbus TCP Server - Improper resource management
CODESYS Modbus is an add‑on for the CODESYS Development System that provides a fully integrated Modbus protocol stack along with diagnostic capabilities. A flaw in the CODESYS Modbus TCP Server protocol stack library results in a vulnerability. When a Modbus TCP server is configured, this vulnerable protocol stack is downloaded to and executed by CODESYS Control runtime systems.
#CVE CVE-2026-35227
https://certvde.com/en/advisories/vde-2026-042/
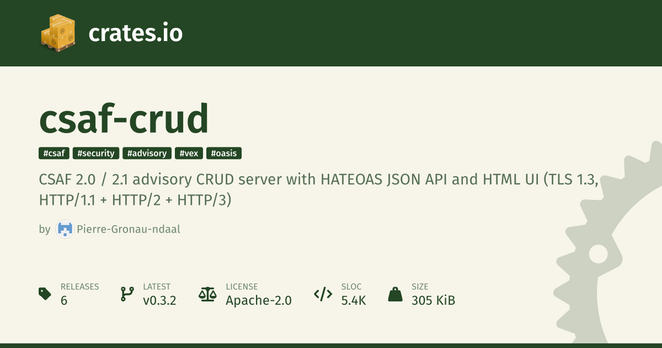
#CSAF https://codesys.csaf-tp.certvde.com/.well-known/csaf/white/2026/advisory2026-05_vde-2026-042.json