Thank you all for your interest in Decoder Loop and Rust reverse engineering training so far!
Our first event is coming up this Friday, November 7th, where @cxiao will be presenting the workshop "Reversing a (not-so-) Simple Rust Loader" at the Ringzer0 COUNTERMEASURE conference (@ringzer0), in Ottawa, Canada: https://ringzer0.training/countermeasure25-workshop-reversing-a-not-so-simple-rust-loader/
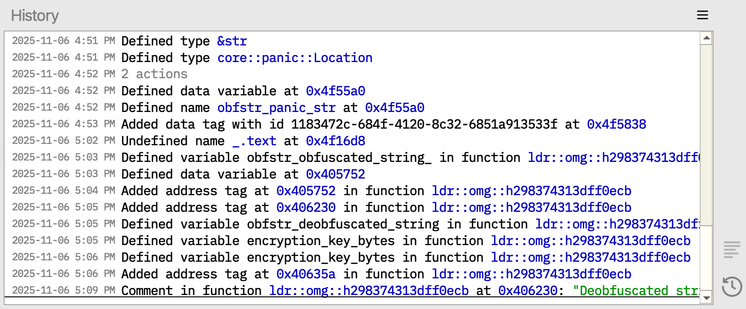
By the end of this workshop, you should know where to get more information about Rust structures and types, know a few tricks for finding interesting landmarks in Rust binaries, and be much more confident in approaching Rust binaries! The workshop will be conducted with @binaryninja , so this is also a great chance to get familiar with Binary Ninja.
We hope to see you there! For more information about upcoming workshops and trainings, keep an eye on this account or sign up on our mailing list: https://decoderloop.com/contact/#training-signup-form
#rustlang #ReverseEngineering #MalwareAnalysis #infosec #reversing #malware #binaryninja #COUNTERMEASURE25 #ringzer0
WORKSHOP: Reversing a (not-so-) Simple Rust Loader // Cindy Xiao
Rust can be challenging for even experienced reverse engineers. We will reverse a simple Rust malware loader found in the wild with obfuscated strings and a decoy payload, making it a good example for learning Rust reversing concepts like threads, dynamic dispatch, and type recovery.