#PrivacyPass #AnonymousCredentials
#PrivacyPass #AnonymousCredentials
#AnonymousCredentials #Unobservability #Unlinkability. #EU_ID_Wallet #eudi #EUID
I have been very sceptic, but recently some people could give me very interesting and convincing insights. And if even the talk at #38c3 and Anja and Thomas are in favor of this, then it can't be that wrong.
https://youtu.be/PKtklN8mOo0?si=DApn26hoxPDTNTVx
38C3 - EU's Digital Identity Systems - Reality Check and Techniques for Better Privacy
Nice, in-depth article on anonymous-credentials and its challenges:
https://blog.cryptographyengineering.com/2026/03/02/anonymous-credentials-an-illustrated-primer/
Anonymous credentials and the related term zero-knowledge proof are core building blocks for privacy-preserving online age verification.
As I understand, the age verification Australia currently requires to upload a legal document (e.g. a driver's license or government ID), or requires proof by doing a "video self". Both techniques would not be privacy-preserving, because in both cases you are sharing personal information with a company (e.g. Meta).
Cryptography like anonymous credentials solves that problem. At least in theory. You can prove your age, and the other side does not learn anything else about you. Still, to roll it out in real-world scenarios there are many challenges (e.g. dealing with attacks like credential theft).
Side-note: the EU proposal is also built on the same type of cryptography: https://ageverification.dev/av-doc-technical-specification/docs/architecture-and-technical-specifications/
Privacy-preserving age and identity verification via anonymous credentials
https://blog.cryptographyengineering.com/2026/03/02/anonymous-credentials-an-illustrated-primer/
#HackerNews #PrivacyPreserving #IdentityVerification #AnonymousCredentials #Cryptography #Engineering #PrivacyTech
Policy, privacy and post-quantum: anonymous credentials for everyone
https://blog.cloudflare.com/private-rate-limiting/
#HackerNews #Policy #privacy #postquantum #anonymouscredentials
Anonymous credentials- rate-limiting bots and agents without compromising privacy
As AI agents change how the Internet is used, they create a challenge for security. We explore how Anonymous Credentials can rate limit agent traffic and block abuse without tracking users or compromising their privacy.
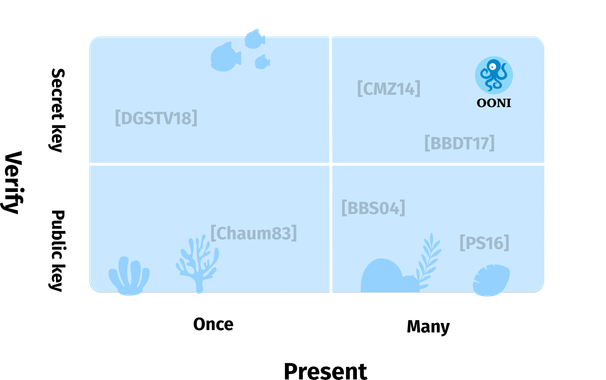
How to protect the OONI dataset from attacks, while preserving the privacy of OONI Probe users?
In our latest blog post, we outline some of the key requirements for OONI's anonymous credential system: https://ooni.org/post/2025-requirements-for-oonis-anonymous-credentials/
Requirements for OONI’s anonymous credentials system
Designing and implementing an anonymous credential system for OONI requires balancing trust in our measurements and the privacy of our users. Our goal is to enrich our measurements with metadata that strengthen their reliability, while maintaining the strong privacy guarantees our users expect.
We are excited to share that we are designing & implementing anonymous credentials within OONI Probe to protect and increase trust in OONI data. 🐙🛡️
Learn more through the literature review on anonymous credentials by Michele Orrù: https://ooni.org/post/2025-probe-security-without-identification/ 💫
Here we go again! This time we have a couple of interesting papers on blockchain-related vulnerabilities, an attack against a lightweight stream cipher, an attack against key-store values, a little something about how hard SBOM¹ can be and a couple of hardware security papers.
* "An Empirical Study of Impact of Solidity Compiler Updates on Vulnerabilities in Ethereum Smart Contracts"
* "Security Analysis of WG-7 Lightweight Stream Cipher against Cube Attack"
* "Prefix Siphoning: Exploiting LSM-Tree Range Filters For Information Disclosure"
* "How to Bind Anonymous Credentials to Humans"
* "Challenges of Producing Software Bill Of Materials for Java"
* "Security Analysis of the WhatsApp End-to-End Encrypted Backup Protocol"
* "The curious case of the half-half Bitcoin ECDSA nonces"
* "X-ray: Discovering DRAM Internal Structure and Error Characteristics by Issuing Memory Commands"
* "Benchmarking and modeling of analog and digital SRAM in-memory computing architectures"
* "(M)WAIT for It: Bridging the Gap between Microarchitectural and Architectural Side Channels"
#Ethereum #Solidity #WG7 #Cryptography #KeyStore #Privacy #AnonymousCredentials #SBOM #Java #SoftwareBillOfMaterials #WhatsApp #E2E #Bitcoin #EDCSA #DRAM #SRAM #SideChannelAttacks
__
¹ Software Bill Of Materials.