Lately, I've realized that I've been working in the AWS space for nearly 10 years.
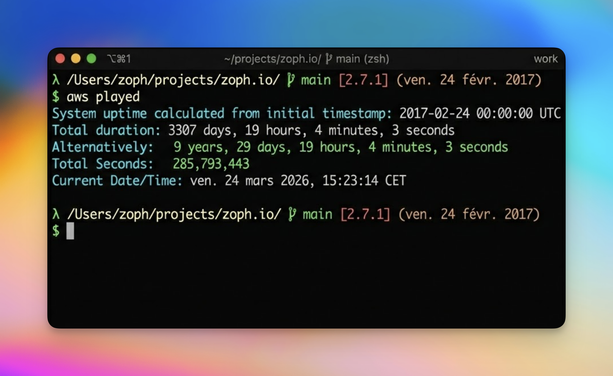
Everything began with this eye-opening moment at an AWSomeDay in Paris (Feb. 24, 2017). I was doing traditional System Engineering at that time, ordering and racking servers, dealing with networking cables, switches, and routers.
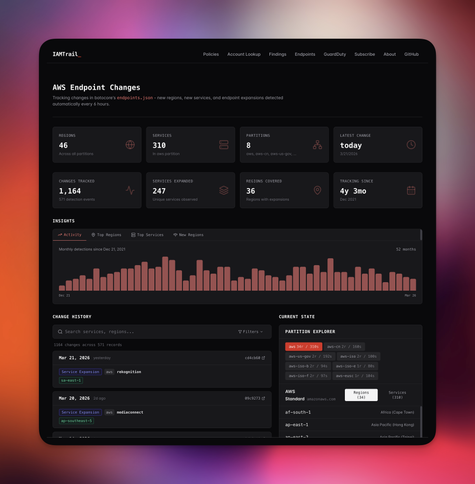
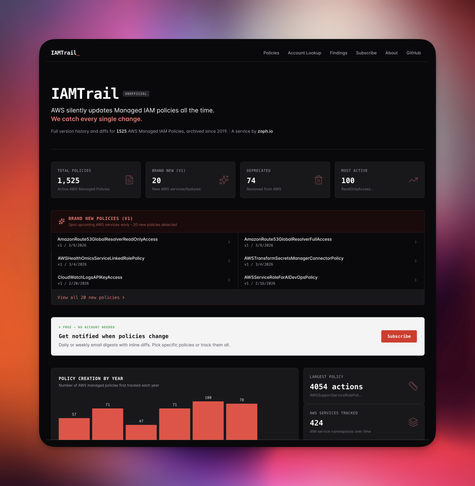
Since then, I’ve been working in AWS Infrastructure and Security. Fell in love with it.
I don't know (yet) what the next eye-opening moment would be.