| Location | France |
x0rz
- 5.4K Followers
- 66 Following
- 106 Posts
PAP (Permissible Actions Protocol) is IMPORTANT, read more here: https://cert.ssi.gouv.fr/csirt/sharing-policy/
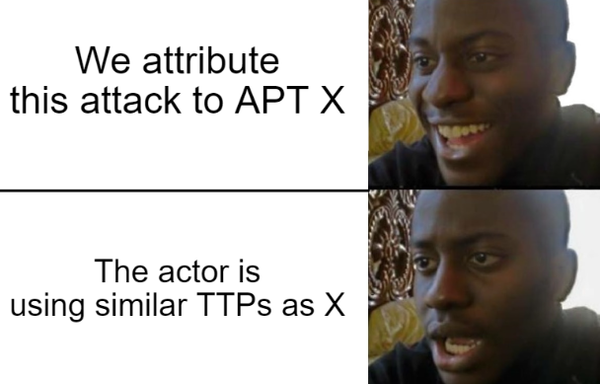
Network information strictly above PAP:GREEN *shouldn't* be blocked. Notifying the adversary you've seen him without thorough investigation is usually bad practice.
I encourage you to get familiar with PAP levels and, depending on the threat, handle information with care. Also, "unknown threat" or unqualified data shouldn't automatically result in blocking, except if you know what you're dealing with.
Here's an example: known malicious scanners should be treated as PAP:WHITE/PAP:GREEN. You can block these with minimal side effects. On the other hand, IP addresses acting as C2 of known strategic threat are generally treated PAP:AMBER. Why? Strategic threat actors usually have more than one foothold inside a compromised network. Not only blocking isn't effective, it's actually counterproductive as it will tip them off. The CERT/SOC advantage is no more, and you'll be in an inconfortable situation having to deal with a threat actor more cautious of its actions.