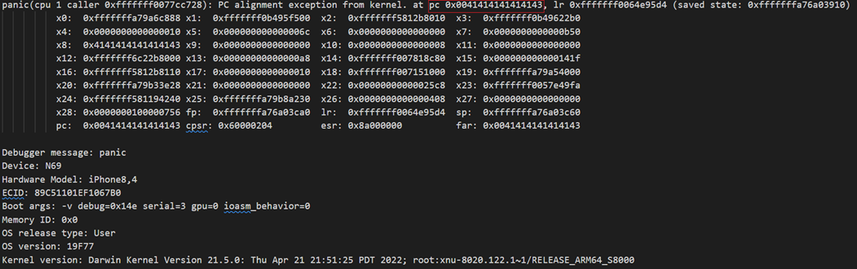
We’re excited to announce that H26Forge is now available at https://github.com/h26forge/h26forge ! We used H26Forge to find video decoding bugs in the iOS Kernel, Firefox, FFmpeg, and hardware decoders, all by generating syntactically-correct, but spec non-compliant H.264 videos. This is joint work with @stevecheckoway and @hovav , and will appear at USENIX Security and Black Hat! (REcon vid coming soon!)
To begin generating videos, you can just build the code, or download a release, and run `./scripts/gen_100_videos.sh`
🧵 (1/3)
GitHub - h26forge/h26forge: Domain-specific infrastructure for analyzing, generating, and manipulating syntactically correct but semantically spec-non-compliant video files.
Domain-specific infrastructure for analyzing, generating, and manipulating syntactically correct but semantically spec-non-compliant video files. - h26forge/h26forge