Hackathon.lu 2026, held in Luxembourg on 14–15 April 2026, once again showed what makes this event special: it is not just a place to present ideas, but a place where ideas turn into code, releases, integrations, datasets, pull requests, and concrete roadmaps.
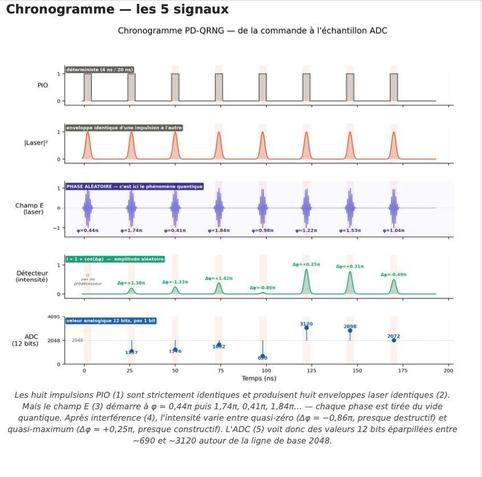
Looking across the all project updates, the overall picture is clear. This year’s edition produced more than thirty concrete project outcome threads, spanning threat intelligence, malware analysis, detection engineering, vulnerability intelligence, graph exploration, forensics, and infrastructure.
Some teams shipped releases on the spot.
Others used the two days to validate designs, harden code, identify weaknesses, or connect previously separate tools into more useful workflows.
The result is a hackathon that delivered not only new features, but also better interoperability across the open-source cybersecurity ecosystem.
#hackathon #luxembourg #opensource #cti #cybersecurity #threatintelligence
🔗 For all the details https://hackathon.lu/2026/04/24/hackathon.lu-2026-outcome/