| GitHub | https://github.com/p- |
Peter Stöckli
- 289 Followers
- 378 Following
- 291 Posts
A huge amount of time is spent simply mapping advisories to build artifacts which organizations care about and while curating with package taxonomies works, the curation cost scales linearly with the number of taxonomies. Practically speaking data collection will be limited in scope as a result.
However, the cost of curating vuln data with commits is decoupled from the cost of mapping those commits to packages. Mapping isn't free, but here's a demo of how it could work
vulnz.ch is a meetup I've been thinking about for a while. It's something I wanted to exist but couldn't find.
The idea is simple: bring together Zurich-based folks for a space dedicated to sharing knowledge about software security. That could mean presenting your analysis of an academic paper you've read, demoing a fork of an open source project you've been experimenting with, or showing off a tool you built during late-night coding sessions.
The first meetup is now being shaped, and the website is up and running. Check out vulnz.ch and sign up if you're interested in joining.
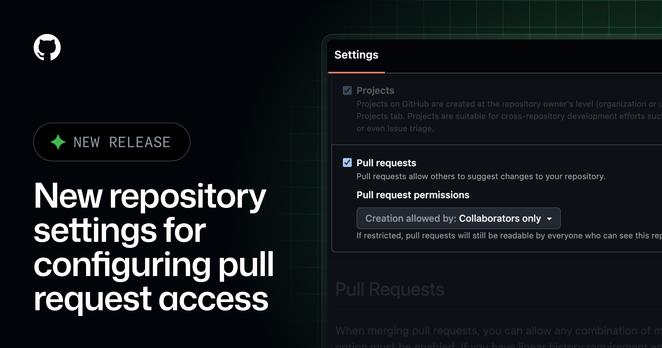
Def going to be using for looooong threads.
https://github.blog/changelog/2026-02-05-pinned-comments-on-github-issues/
“To stress test it, I tasked 16 agents with writing a Rust-based C compiler, from scratch, capable of compiling the Linux kernel. Over nearly 2,000 Claude Code sessions and $20,000 in API costs, the agent team produced a 100,000-line compiler that can build Linux 6.9 on x86, ARM, and RISC-V.”
🤯
We've just hit a very important milestone - our XSS Cheat Sheet now has 1337 vectors!
Browse them here: https://portswigger.net/web-security/cross-site-scripting/cheat-sheet
Here are three lines from my AGENTS.md that make agents a lot better with Go.
Go has great CLI tools, but many people don't know about them, and so agents are not trained to reach for them.
Maybe the Go project should maintain a Go development skill?