Tony Shannon
- 101 Followers
- 336 Following
- 230 Posts
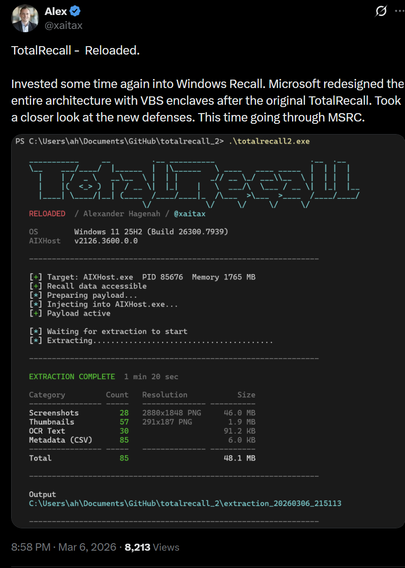
So @xaitax has cracked Microsoft Recall, he's got access to the encrypted database and has automated dumping of screenshots and all text from screenshots.
I've looked at most recent Recall and yep, you can just read the database as a user process. The database also contains all manner of fields which aren't publicly disclosed for tracking the user's activity.
No AV or EDR alerts triggered, world's #1 in infostealer 😅
* you can just read it in plain text
[EDIT: now sorted thank you SO MUCH!]
Heads up my dudes, my son needs to do work experience this summer and he's a programmer. Nearly 15, can do 3 decent languages, main in Java, been programming since 4. All he wants to do is be a developer. Anyone offer work experience these days? Two weeks in July. London or Dartford way or anywhere in between. Ta! Retoots appreciated!
Palantir Sues Swiss Magazine For Accurately Reporting That The Swiss Government Didn’t Want Palantir
https://www.techdirt.com/2026/02/27/palantir-sues-swiss-magazine-for-accurately-reporting-that-the-swiss-government-didnt-want-palantir/
Please note that Palantir would rather that you didn't share this story, it makes them look even more stupid if you do...

Palantir Sues Swiss Magazine For Accurately Reporting That The Swiss Government Didn’t Want Palantir
If you run a company whose entire value proposition is the ability to see patterns, predict outcomes, and connect dots that others miss, you’d think someone in the building might have flagged…
I have had people tell me cybersecurity is essentially being taken out of Connect (yearly goal reviews), which was Microsoft's big commitment to Congress as part of Secure Future Initiative.
Brad Smith testified to US Congress everybody had to demonstrate what they'd done for security - but it's been watered down now to the point where it basically doesn't exist any more, I'm told. MS haven't told public about the changes.
It's one to watch, to see if things start to backslide at MS w/ cyber.
Knowledge Commons (@[email protected])
We’re currently experiencing a widespread outage affecting access to Knowledge Commons, including KCWorks and all user sites. Our team is actively investigating and working to restore service as quickly as possible. Thanks for your patience, and we're sorry for the inconvenience.
MongoDB have a blog out about #MongoBleed
Notably:
- Internal find at MongoDB
- they notified customers of the issue and patch availability on December 23rd
- A security vendor published technical details on December 24th, Christmas Eve
- Somebody at Elastic, a direct competitor, published an exploit with full secret extraction feature on December 25th, Christmas Day
That was an impossible situation for orgs - the security industry poured fire on them and set their own customers on fire.
A Christmas lesson:
Cyber people probably shouldn't post full chain exploits which automate stealing secrets on Christmas Day for new vulns in direct competitor products.
I mean, people can post whatever they want.. it would just be nice to have a holiday with family and all, rather than arming teenagers.
https://www.404media.co/flock-exposed-its-ai-powered-cameras-to-the-internet-we-tracked-ourselves/