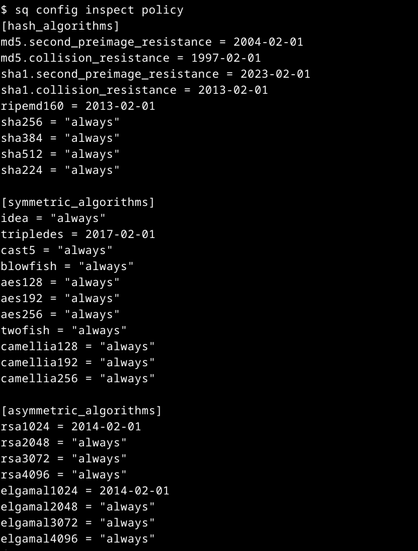
Whenever Sequoia does a security sensitive operation, it first consults a policy. A policy says what cryptographic algorithms and constructs are allowed. SHA-1 is disallowed by default, for instance. The policy is first loaded from /etc/crypto-policies/back-ends/sequoia.config , but it can be overridden by the user's configuration file. You can inspect the effective policy using the following command:
$ sq config inspect policy
https://docs.rs/sequoia-policy-config/latest/sequoia_policy_config/