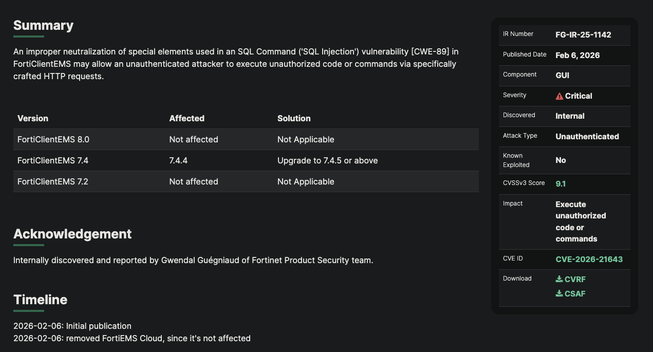
🚨 CVE-2026-21643 an SQL Injection vulnerability (CVSS 9.8) is seeing active exploitation in the wild as reported by @DefusedCyber
Vulnerability detection script available here:
https://github.com/rxerium/rxerium-templates/blob/main/2026/CVE-2026-21643.yaml
This vulnerability currently only affects FortiClientEMS 7.4.4 and it is recommended that you upgrade to 7.4.5 or later as reported by Fortinet:
https://fortiguard.fortinet.com/psirt/FG-IR-25-1142