| Personal Site | https://www.mccune.org.uk/ |
| Blog | https://raesene.github.io/ |
| Container Security Site | https://www.container-security.site |
| GitHub | https://github.com/raesene/ |
Rory McCune
- 1,033 Followers
- 341 Following
- 784 Posts
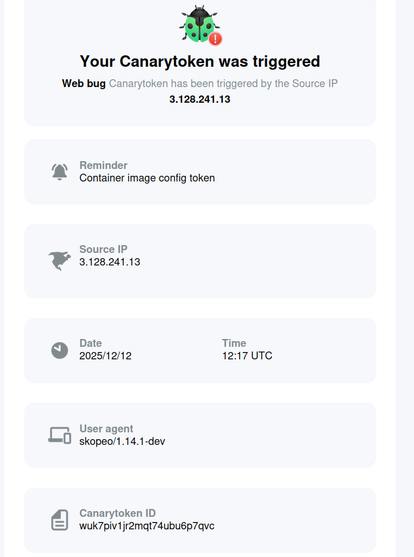
So, some time ago I was playing with the idea of adding tracking to container images (https://raesene.github.io/blog/2023/02/11/Fun-with-Containers-adding-tracking-to-your-images/) .
the idea is that you add a URL to the config section of an OCI image and then whenever the image gets pulled, the URL gets called.
I can't remember exactly where I uploaded the image with the canary token in it, but someone's been pulling that image regularly for a while now and I get a ping whenever they do :)
Definitely a day to patch your git installs. There's a PoC for a new git CVE.
I wanted to test it but we all know you don't run PoC code on machines you care about... literally 1 min later on a fresh https://labs.iximiuz.com/ playground test confirms it works!
I'm just refreshing a #kubernetes security talk today, so checking on numbers of exposed clusters. Interesting and not great that the number of cluster operators exposing their API server to the Internet is still going up.
Last time I checked it was 1.4M, now (based on this query) , it's almost 2M!
A #kubernetes distribution issuing a system:masters cert with a 15 year expiry is definitely.... an interesting choice.
At least they do offer the possibility of revoking by rotating the CA key and requiring all new certs.