@trashpanda @ahf Hi, thanks for the ping and interest!
It isn't very easy to answer since things are a bit mixed up here and on the TorPlusVPN page.
Maybenot is a *framework* for traffic analysis defenses, meaning that what Maybenot can and cannot help with depends on what kind of defenses are running in the framework. As @ahf mentioned, what Arti can offer here is tbd as Arti relay hacking progresses further.
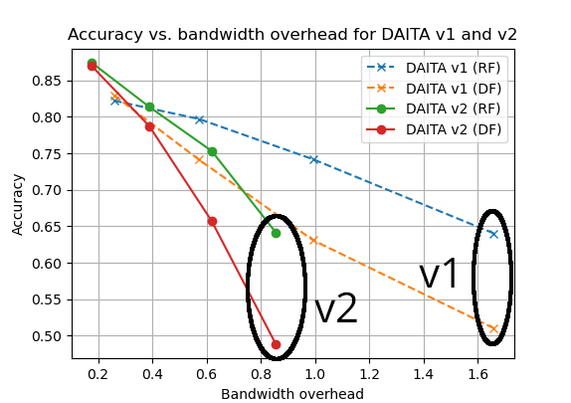
There is one significant deployment of Maybenot now with DAITA and Mullvad VPN, https://mullvad.net/en/vpn/daita . In DAITA, we aim to make Website Fingerprinting attacks harder, create fake activity when the VPN is not used (fake background traffic), and do some more general tweaks to WireGuard (constant-sized packets and mess with NetFlow, based on Tor's connection-level padding). Please note that DAITA is for VPN traffic, so the connections are long-lived and typically carry all traffic from a system. DAITA is also very much a work in progress, but we're shipping and iterating. To get an idea of where we're heading, stay tuned for the PDF of "Ephemeral Network-Layer Fingerprinting Defenses" at https://petsymposium.org/2026/paperlist.php soonish and see fun machine generation tooling at https://github.com/maybenot-io/maybenot (use https://github.com/maybenot-io/maybenot/tree/main/crates/maybenot-cli).
If you compare Tor and WireGuard/OpenVPN/SSH, Tor already does connection-level padding (mess with NetFlow as mentioned), chops traffic into fixed-sized cells, and creates many isolated short-lived circuits through the large and distributed Tor network. This should not be underestimated in terms of how it messes with *reliable* traffic analysis for network adversaries who want to figure out what you're doing in Tor. It's a significant bar.
Now to get closer to answering the question: would/could Maybneot + VPN/SSH make VPN/SSH fingerprinting harder? Short answer is yes, if you create machines for this purpose. I don't think Website Fingerprinting, as in the TorPlusVPN wiki is the most relevant threat here. WF is messy and rich in false positives. If the goal of the adversary here is to detect that you're using Tor within a VPN/SSH tunnel, this is more in line with all the cool work on anti-censorship, where Tor traffic is tunneled to hide the fact that Tor is used. The relevant fingerprinting attacks become, e.g., https://www.ndss-symposium.org/wp-content/uploads/2025-966-paper.pdf .
So the TL;DR: Hide using Tor? Use the cool anti-censorship tools! They are designed to make detecting Tor use difficult. Protect against someone fingerprinting what is done over Tor? Maybenot can help here in Arti in the future (DAITA helps today), but remember that Tor helps today as-is compared to regular VPN/SSH tunnels.