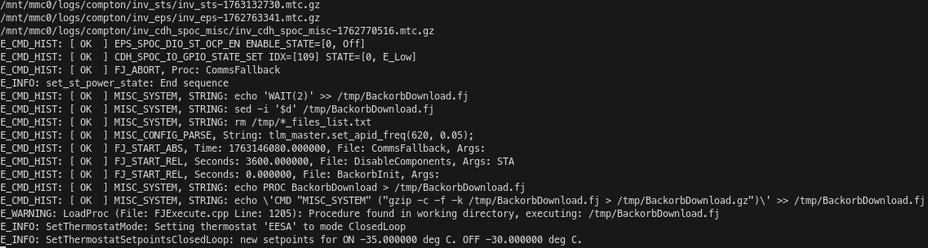
did additional reverse-engineering, and I wanted to revisit this and dig deeper in the telemetry. In this post I go over some details of the flight software, including file downlink, logs, and on board scripting. I also find some quaternion data and gyroscope data that are a good match, plus other quaternions that I don't know how to interpret.
satcat, but not the NORAD kind 🛰️🐱
hacking video games, space systems, and other rocks that try to think
CTF w/ ENOFLAG
operating BEESAT-1 @ TU Berlin
🏳️🌈🏳️⚧️
| pronouns | she/they |