I kicked off the new year by adding 2,087 cybersecurity products to CybersecTools.
For the past 2.5 months, I’ve been working on ways to research, validate, and enrich data for every product:
→ Technical features (what they actually do)
→ Integration capabilities (what they connect to)
→ Company intelligence (who builds them)
→ Market positioning (where they fit)
Why go this deep?
Because right now, great cybersecurity companies solving real problems often go unnoticed.
They’re creating products that could change how security operations work.
They’re addressing real challenges that CISOs deal with every day.
They’re innovative, focused, and deserve a chance to succeed.
But they’re still hidden.
Hidden behind Gartner quadrants that keep showing the same 10 names.
Hidden behind analyst reports that favor big enterprise vendors with huge budgets.
Hidden behind marketing noise from companies that can pay for more visibility.
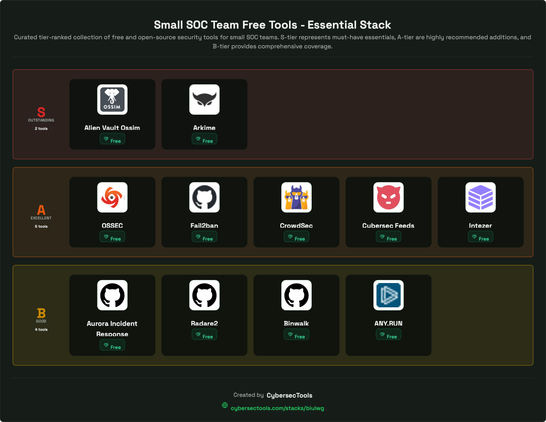
CybersecTools is here to help security teams find solutions that truly fit their needs.
But there’s another way to use this data.
With validated information on 5,688 products (their features, integrations, positioning, and company details) you have more than just a discovery platform.
You have the most comprehensive view of the cybersecurity competitive landscape.
This means the same data that helps security teams pick the right tools can also help cybersecurity companies understand their market, analyze competitors, and position themselves to succeed.
That’s what I’m working toward. More updates soon.
Are you building a cybersecurity company and looking for insights to get ahead of your competitors? Reach out.