Niels
- 69 Followers
- 32 Following
- 211 Posts
RE: https://oldbytes.space/@feoh/116687129039392818
Advice I was given in my youth:
Print your slide on a full piece of paper. Put the paper on the ground. Stand on a chair.
If you can’t easily read your slide, neither can the person at the back of the room.
It flummoxes me that 30 years into using computers to show slides, tiny fonts in slide is *still* widespread practice.
Almost two years ago I presented on the challenges that come with self hosting things for friends and family when you're not available anymore.
Today at RIPE92 (@ripencc) Robert Kisteleki presented an initative to gather information, best practices, etc on this topic.
You can find his presentation here: https://ripe92.ripe.net/programme/meeting-plan/sessions/103/7PEF7V/#robert-kisteleki.
Video of my presentation: https://www.youtube.com/watch?v=K3Ocy1AyLpg, slides: https://nlnog.net/events/past-events/nlnog-day-2024/presentations/NLNOG2024-05-Teun_Vink_-Your_Digital_Legacy.pdf.
Please join this initiative so we can create a set of best practises!
Yesterday, a kernel flaw affecting many different Linux distributions
was announced: https://copy.fail. This issue allows unprivileged users to gain root privileges on unpatched systems. Since no updated kernel packages have
been released yet by Ubuntu, we have implemented the suggested workaround on all NLNOG RING nodes.
We have no indications that any RING nodes were compromised before we
implemented the fix. Should you notice any signs of the contrary, please
let us know.
I found a chain of vulnerabilities in systems at RIPE NCC, operator of one of five global RPKI trust anchors. A single click on an ordinary-looking link was enough to disconnect a network from the internet.
My entry points were debugging fields in DNS and crafted TLS certificates. From there, I escalated to the RPKI Dashboard, which controls which networks are authorised to announce your IP addresses to the internet, and the RIPE Database, which stores routing policy. All vulnerabilities have been fixed.
Full write-up: https://mxsasha.eu/posts/ripe-ncc-rpki-exploit-chain/
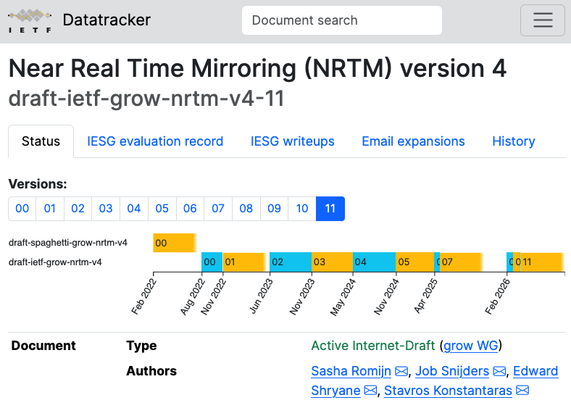
Just over 4 years after publishing the first draft, NRTMv4 has been approved by the IESG! This was my first ever IETF draft. This new protocol dramatically improves Internet Routing Registry security and reliability.
All that remains now is the RFC Editor process. Four authors went through 11 versions, 25 reviewers/implementers, dozens of comments, and 5 interoperable implementations. Catch my talk at the #RIPE92 database working group to learn more.
"When I look at Nextcloud I see five million lines of PHP."
"Yeah, well, I just see one Docker image."
We have another event planned: on June 5th we will be organising 'Lekker Weer NLNOG 2026', a combination of interesting talks followed by drinks and good food!
For more details check out https://nlnog.net/events/lekker-weer-nlnog-2026/
We hope to see you all there!
We cannot search our internal code repository, because that requires an enterprise license.